Intelligence Supply Chain
The operating model that turns agents, copilots, and AI services into repeatable business capability—without runaway cost or risk.
AI won’t scale because model Intelligence Supply Chains get smarter. It will scale because enterprises learn to manufacture intelligence—reliably.

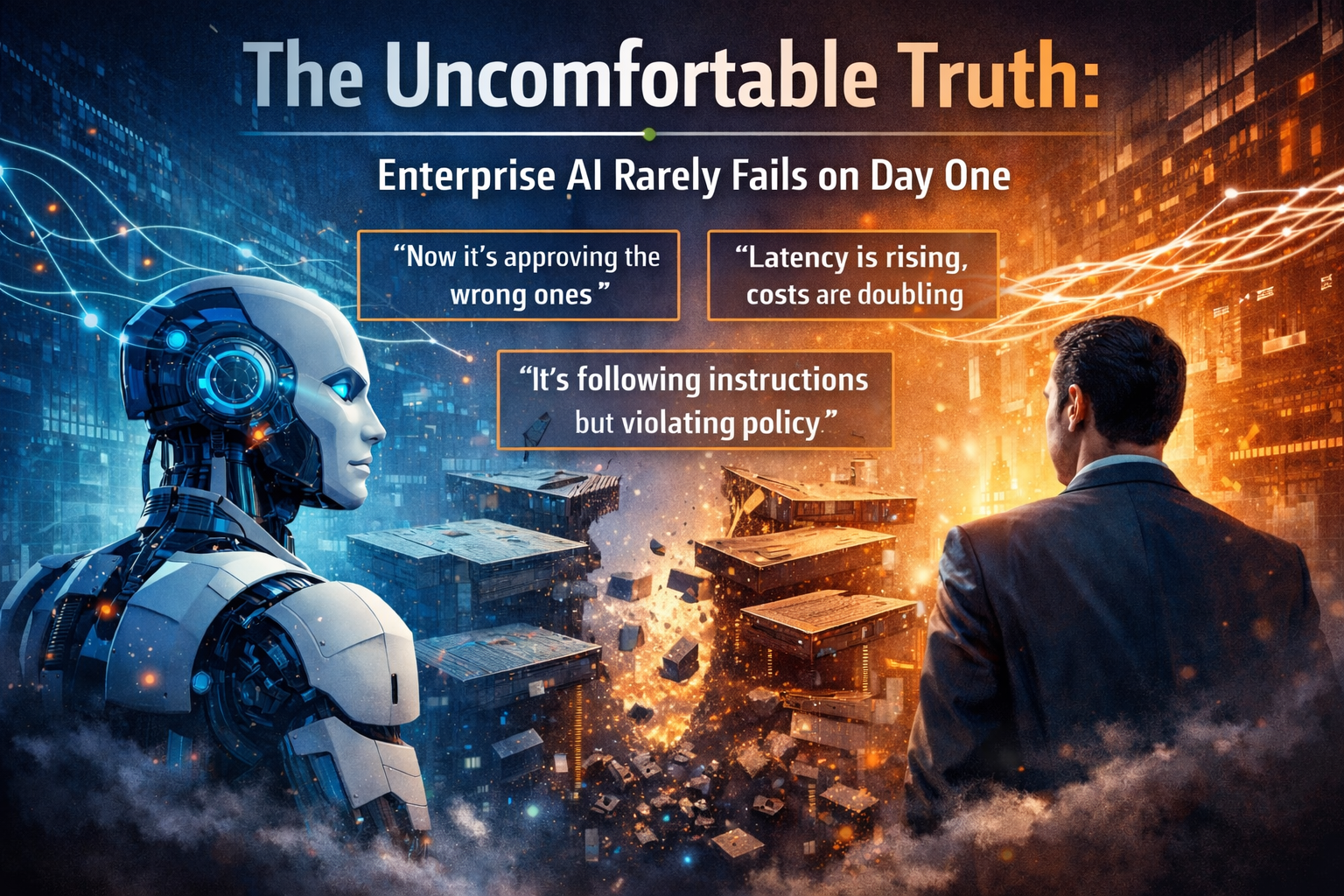
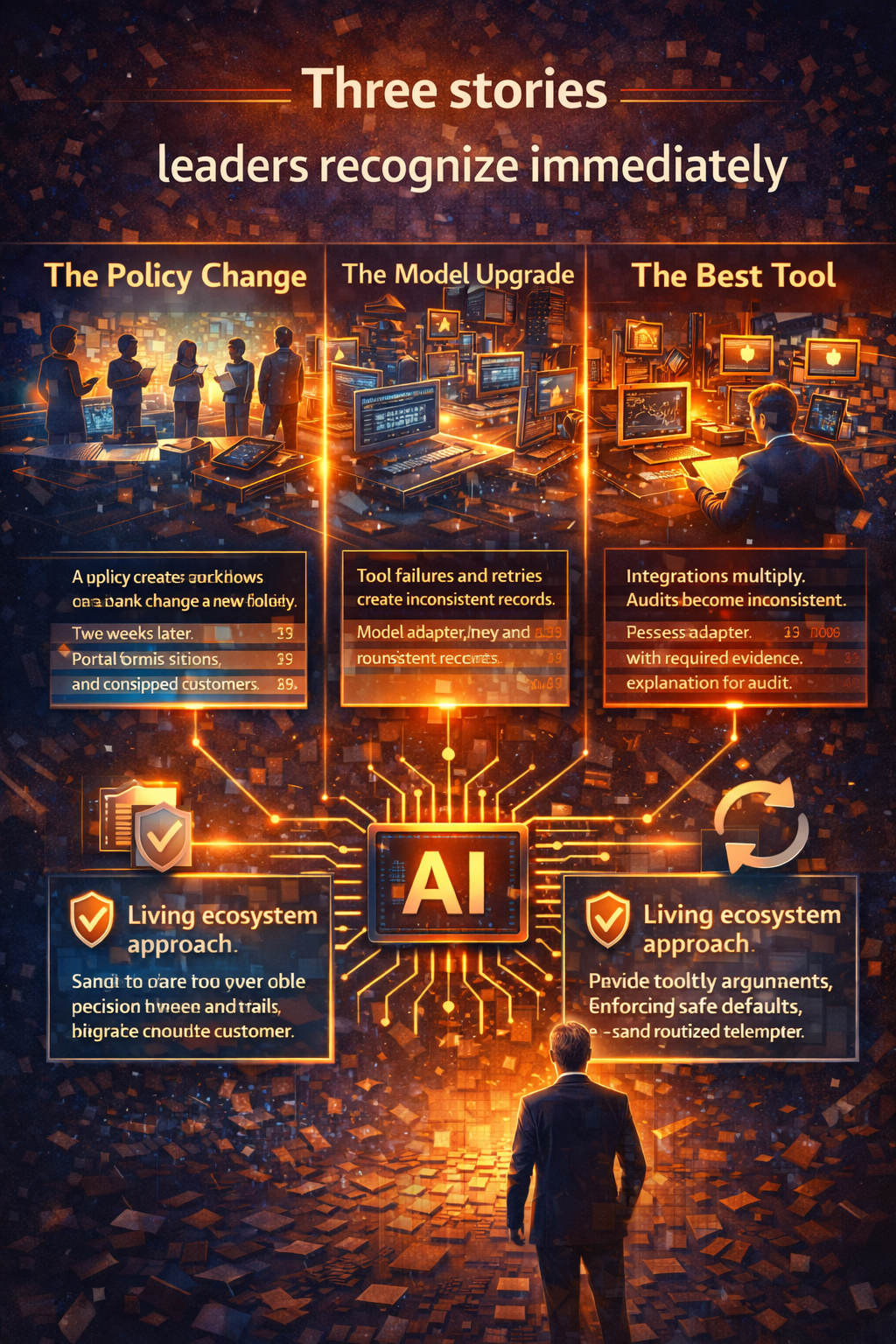
A story you’ve seen before (even if your enterprise won’t admit it)
It starts with a pilot that works.
A team launches an AI assistant to reduce workload. Early numbers look great: fewer tickets, faster response times, happier stakeholders.
Someone declares it “the future.” Another team asks for the same thing.
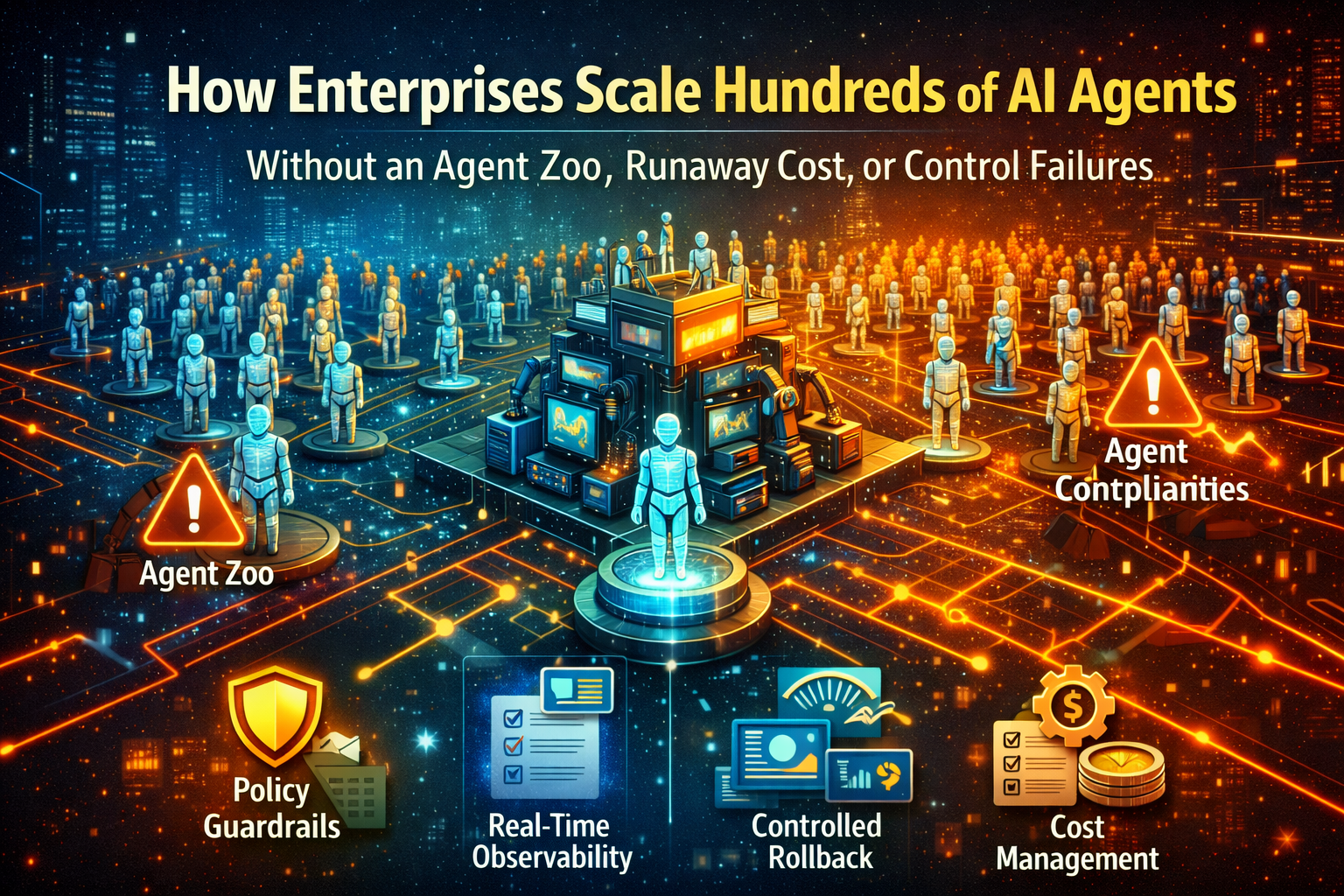
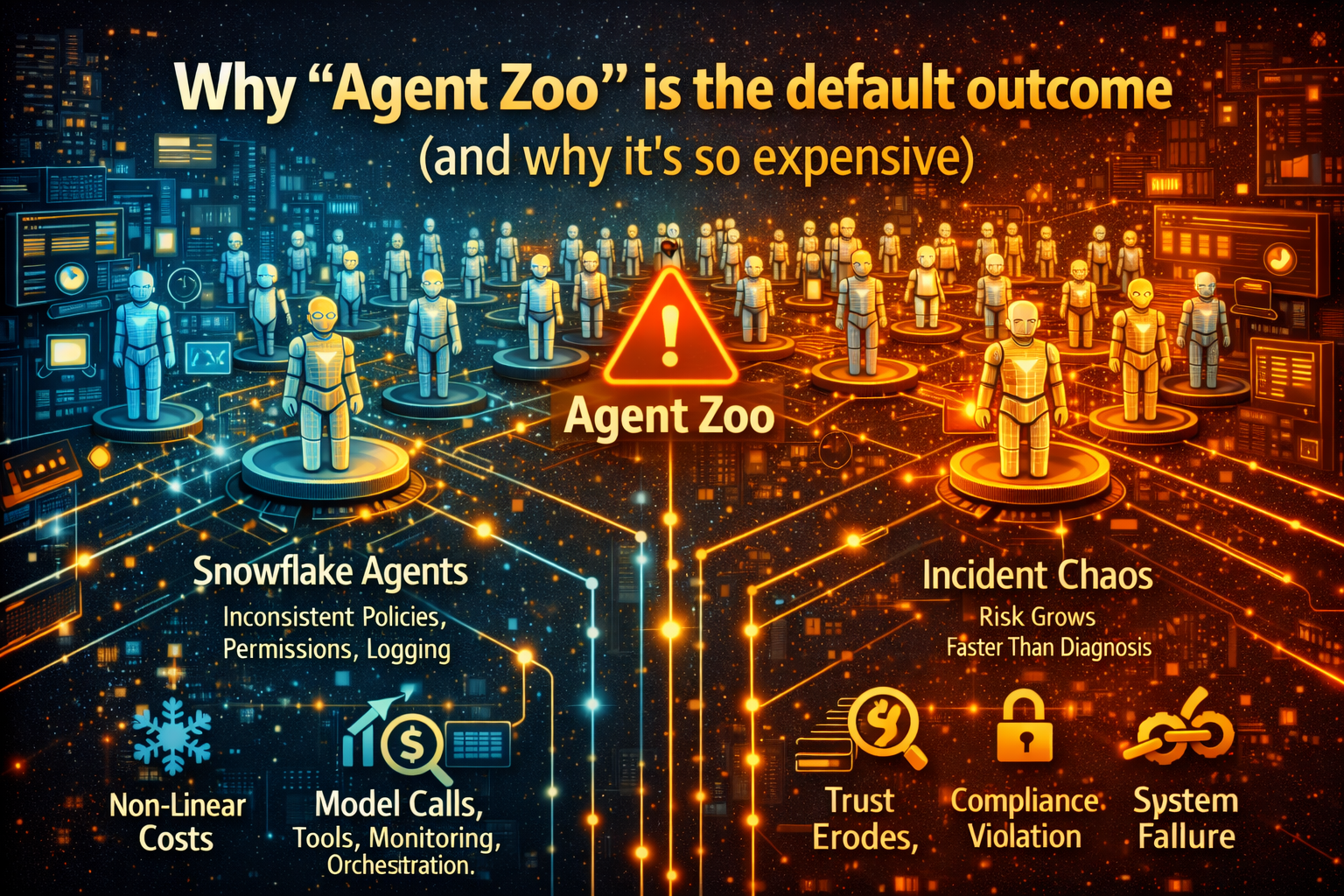
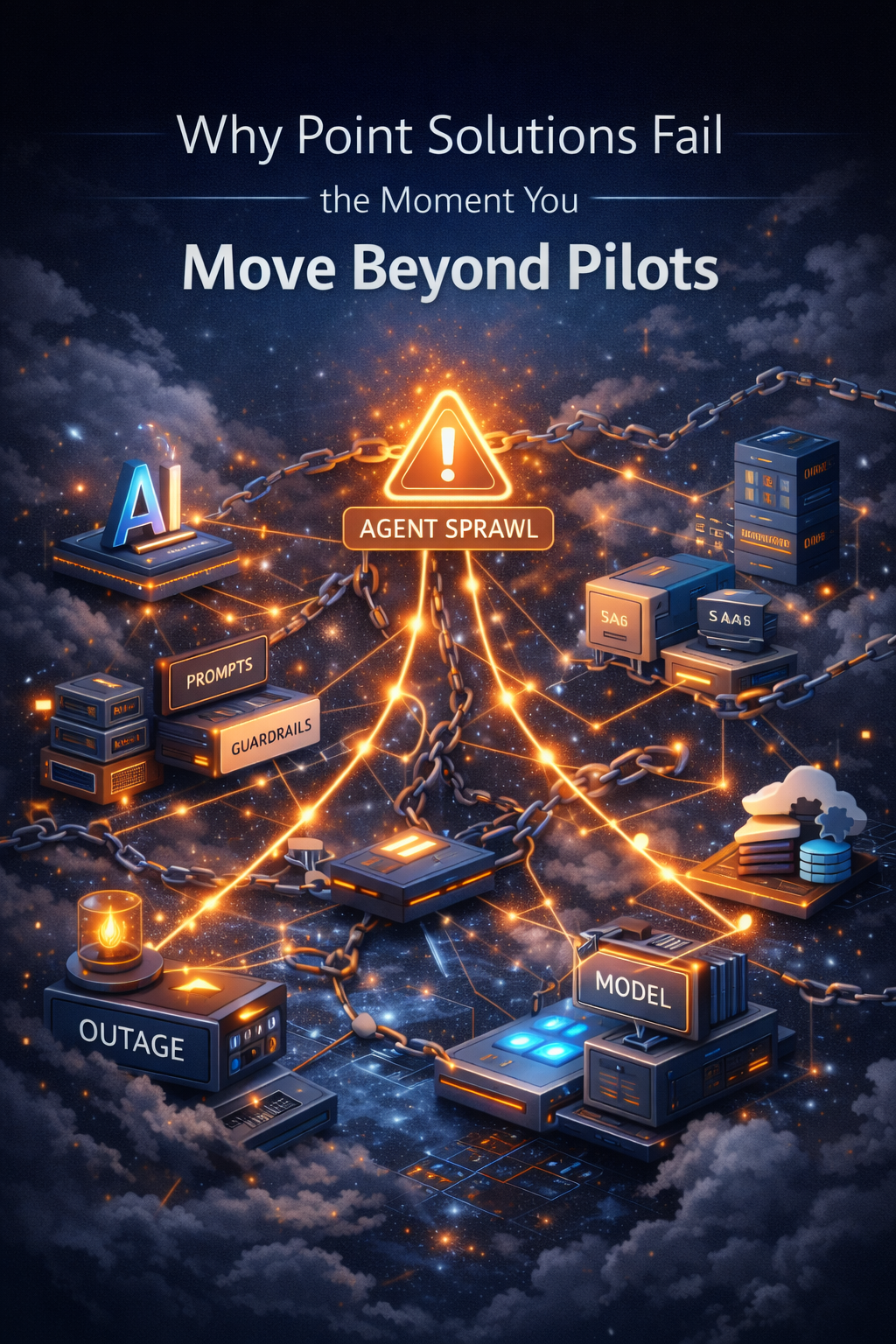
Then a third team. Soon there are dozens of assistants and early-stage agents, each built slightly differently—different prompts, different guardrails, different tooling, different vendors, different monitoring, different cost patterns.

Nothing is “broken.”
But you can feel the system becoming brittle.
Then the quiet symptoms appear:
- Costs rise in ways no one can explain.
- Agents behave differently after minor policy updates.
- A workflow that was safe in a sandbox becomes risky in production.
- Teams ship faster—but governance lags behind.
- Everyone rebuilds the same components (auth, logging, approvals, tool wrappers), and no one agrees on a standard.
At that moment, the organization realizes something uncomfortable:
It didn’t adopt AI.
It adopted a new production system—without building the factory.
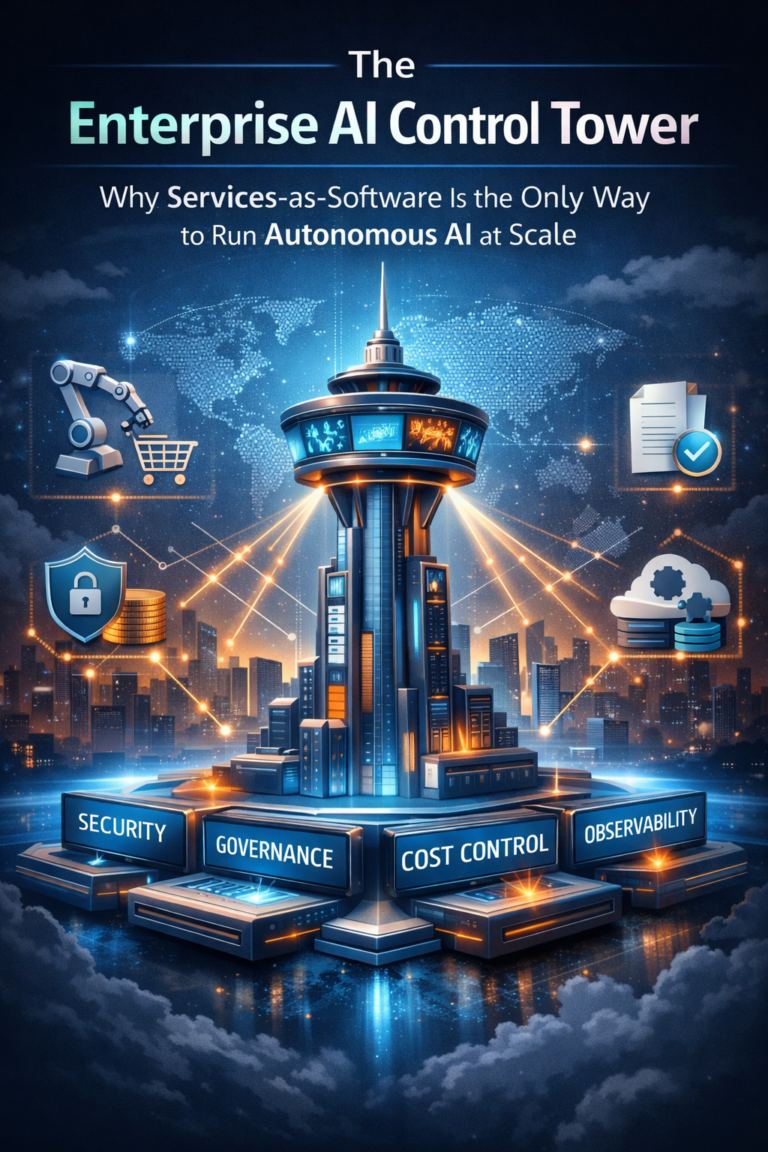
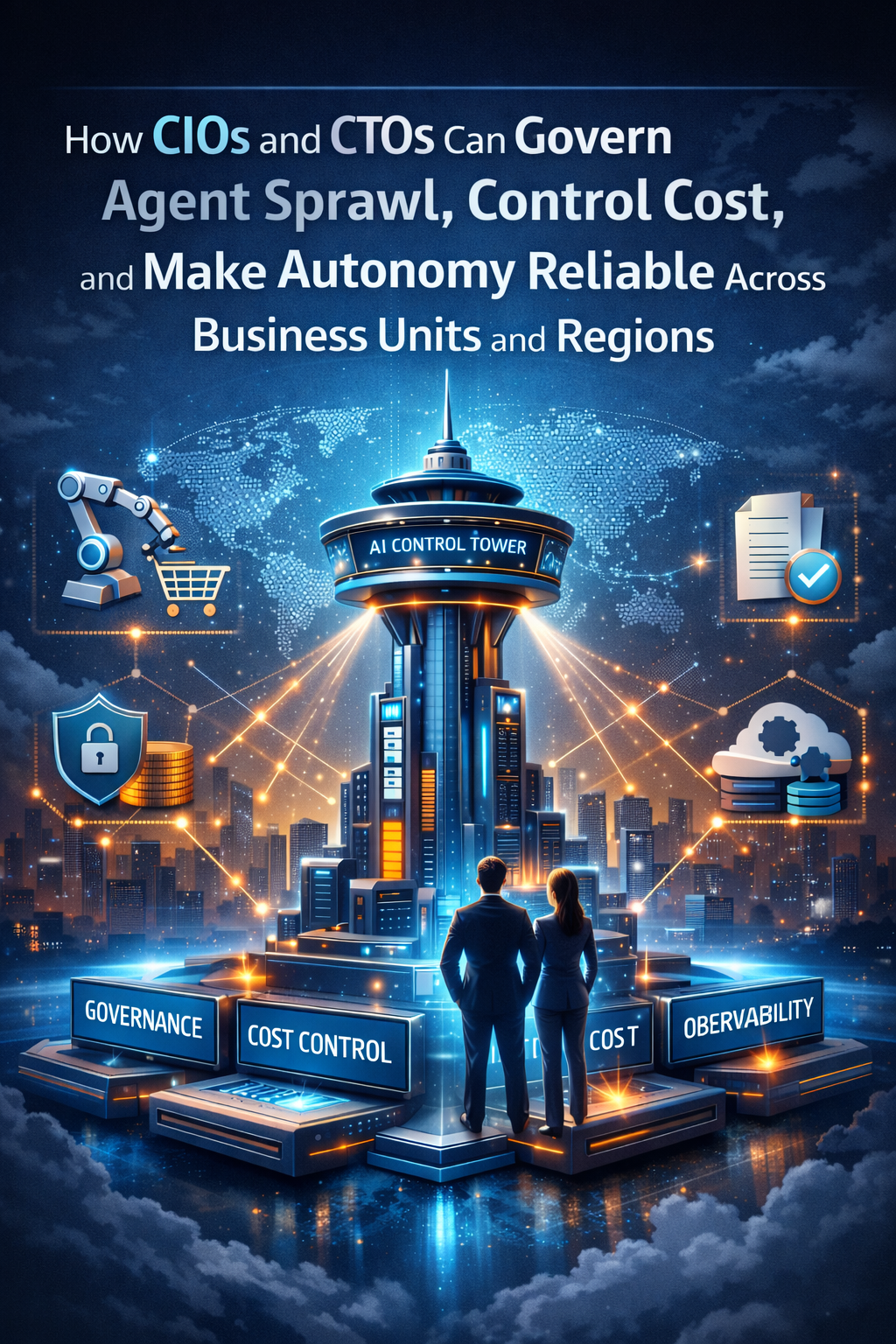
That is why enterprises are moving past the “AI platform” framing and toward something more industrial: an Intelligence Supply Chain.

The market signal executives can’t ignore
This isn’t a theoretical shift. It’s a survival shift.
Gartner predicts over 40% of agentic AI projects will be canceled by the end of 2027 due to escalating costs, unclear business value, or inadequate risk controls. (Gartner)
Notice what’s missing from that list: “the model wasn’t smart.”
The reasons are operational. Economic. Governance-related.
Which is exactly why the winners are changing the question from:
“Which AI platform should we buy?”
to
“How do we produce, govern, and run AI—reliably—every day?”
That is an operating model question.

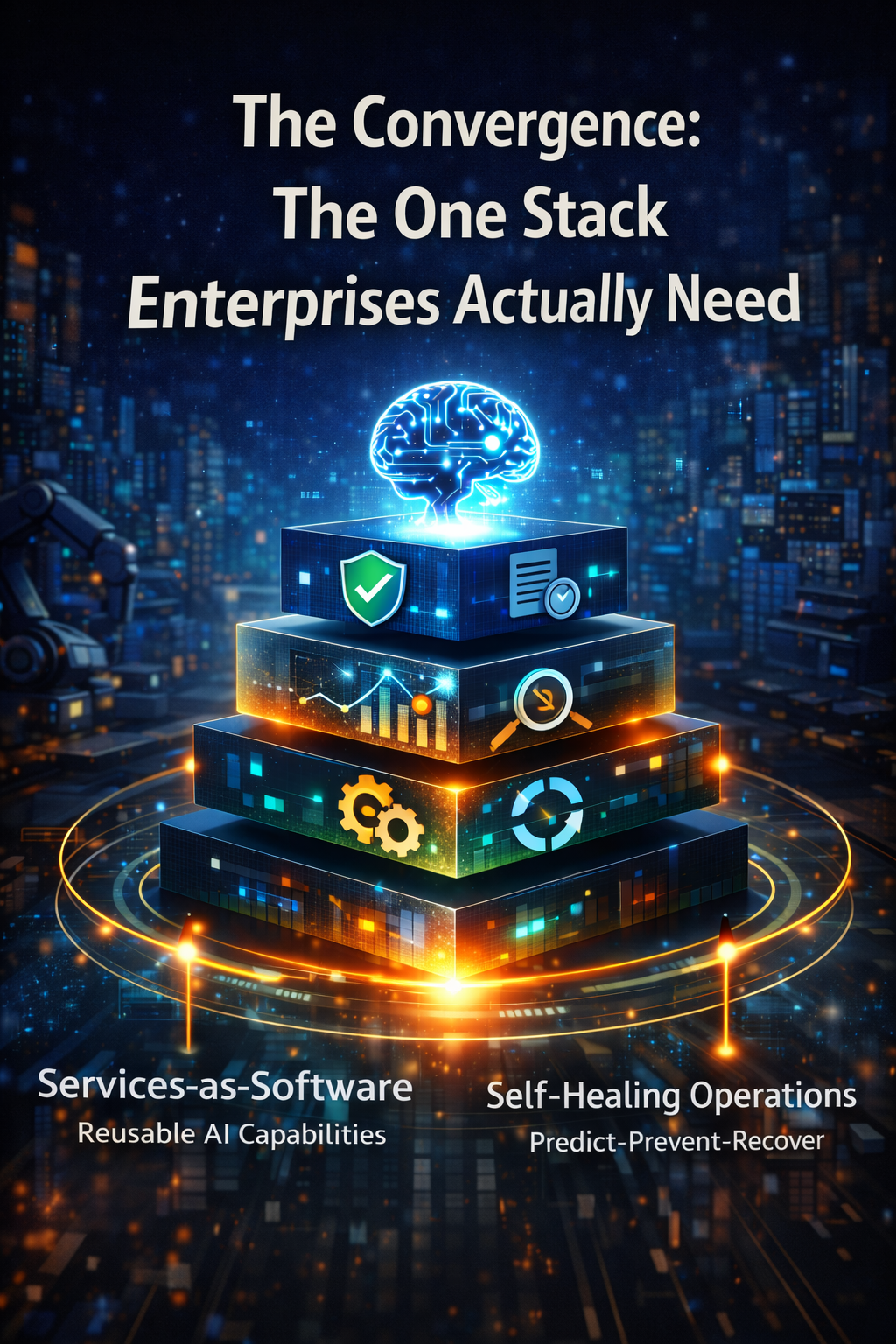
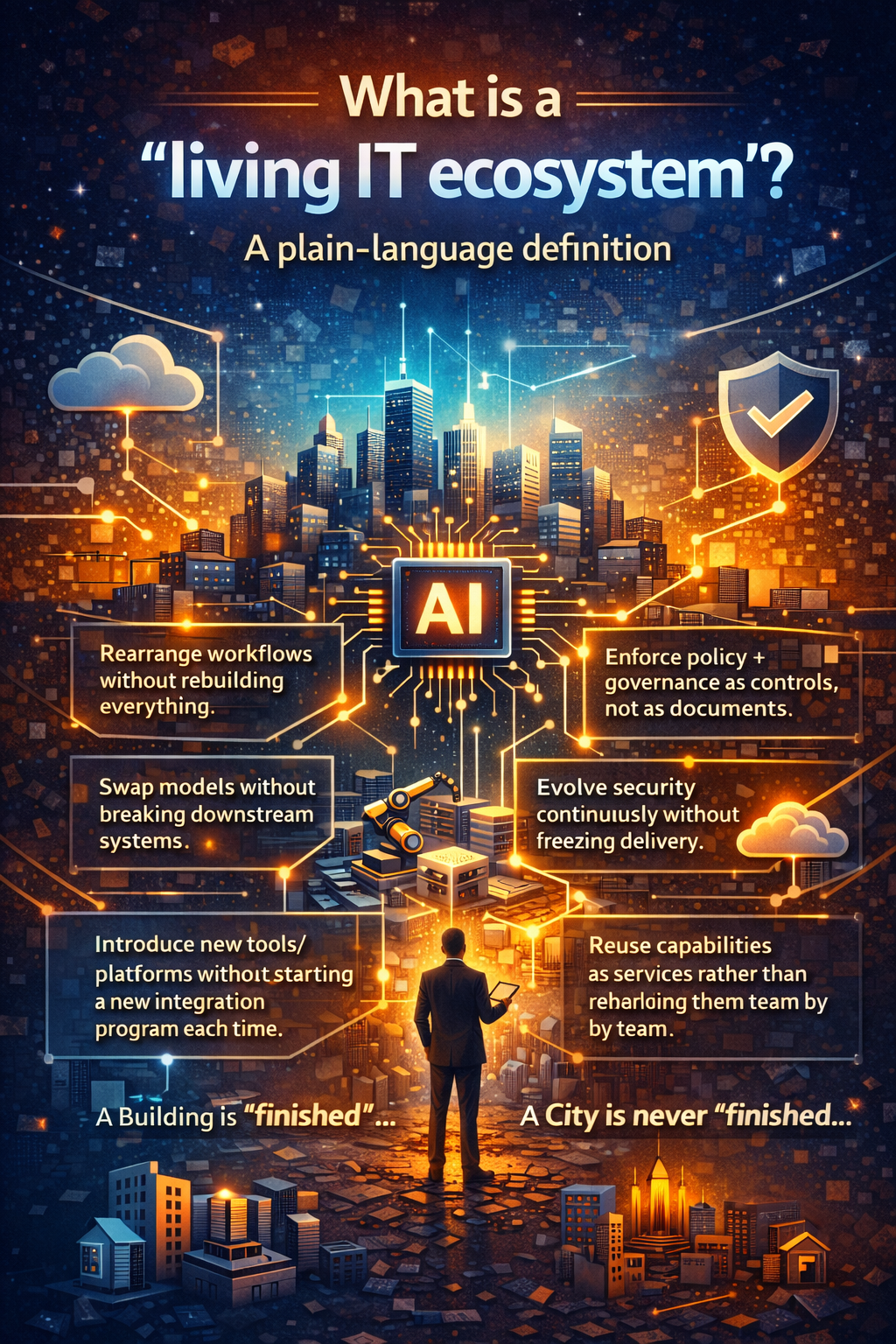
What an “Intelligence Supply Chain” actually means (plain language)
An intelligence supply chain is an end-to-end system that lets an enterprise produce, verify, deploy, and operate intelligence with predictable:
- quality (it behaves as intended)
- trust (it stays within policy)
- economics (cost is measurable and controllable)
- reuse (capabilities are shared, not reinvented)
- resilience (it can be monitored, corrected, rolled back)
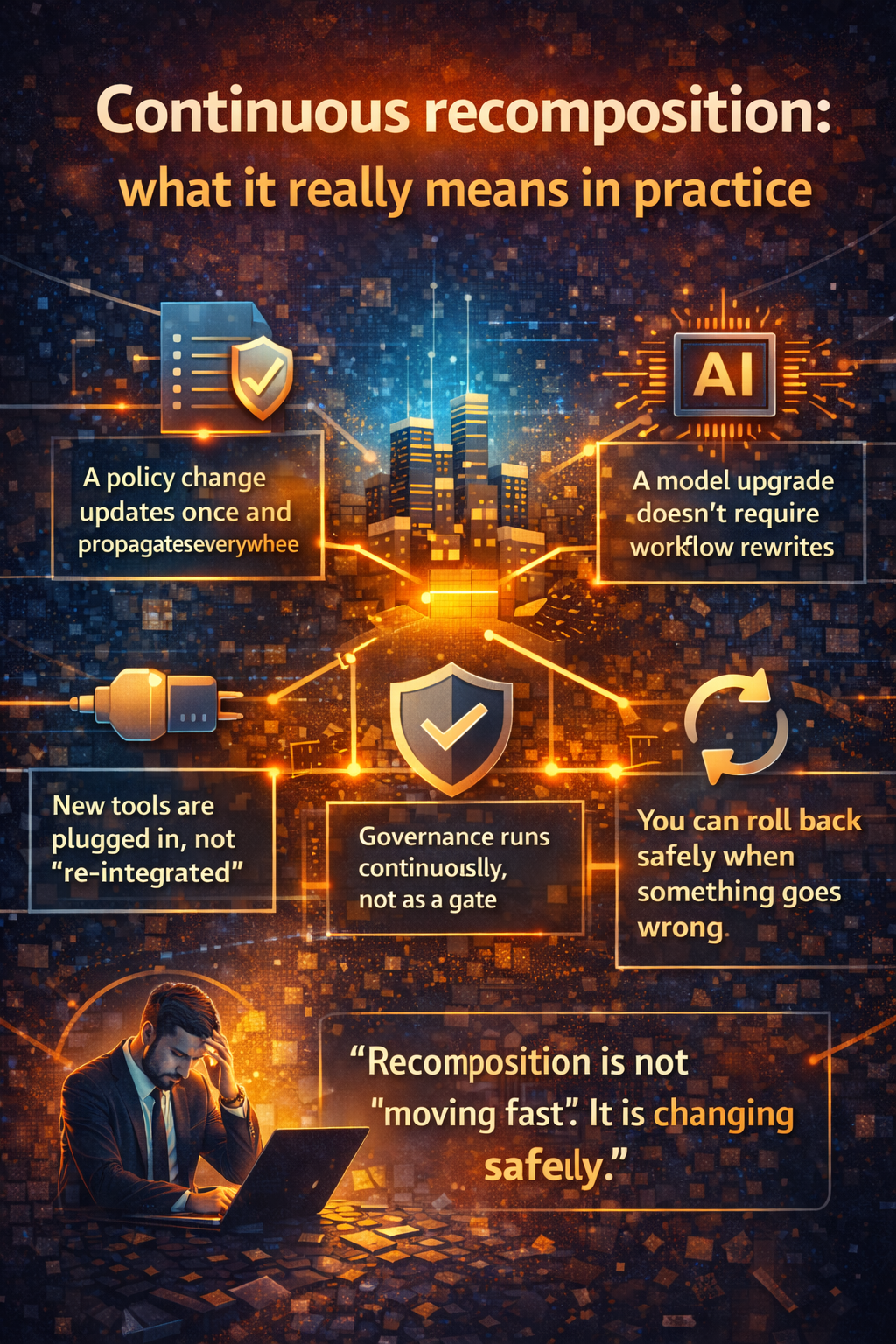
It’s the shift from building AI to manufacturing intelligence.
And supply chain thinking forces one discipline that separates serious enterprises from experimenters:
Every unit of intelligence must flow through:
design → test → govern → cost-control → deploy → monitor → improve
Not once. Continuously.

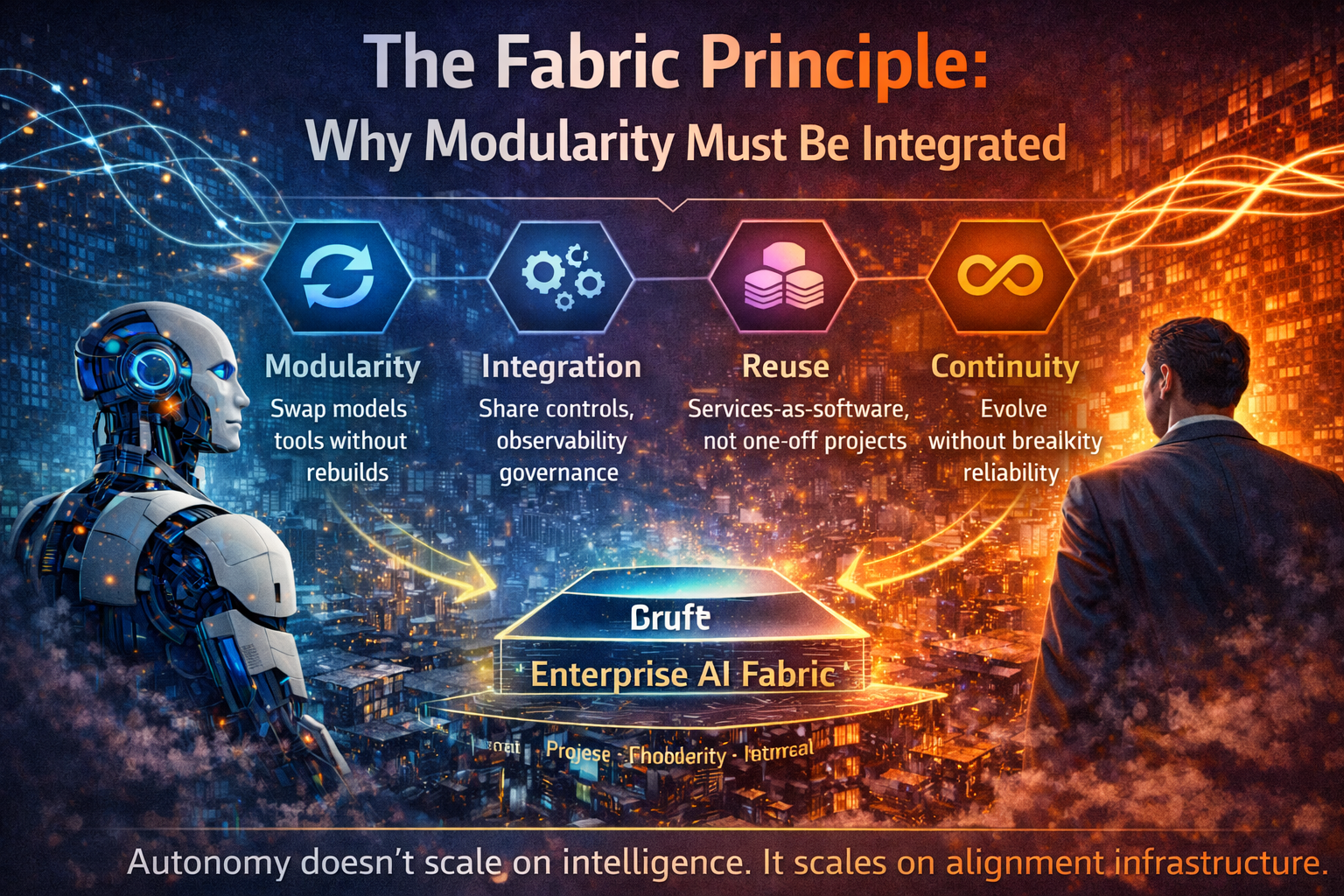
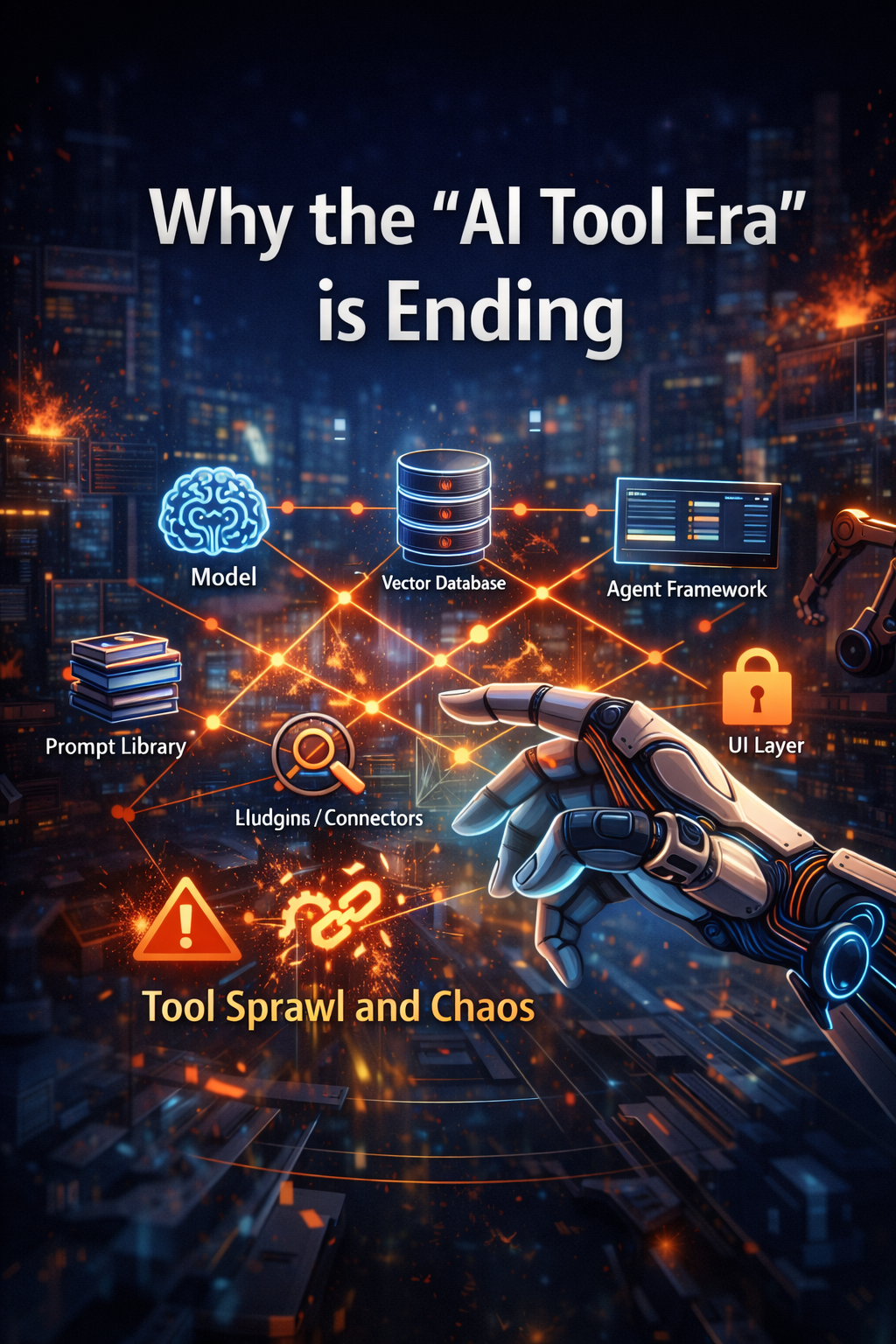
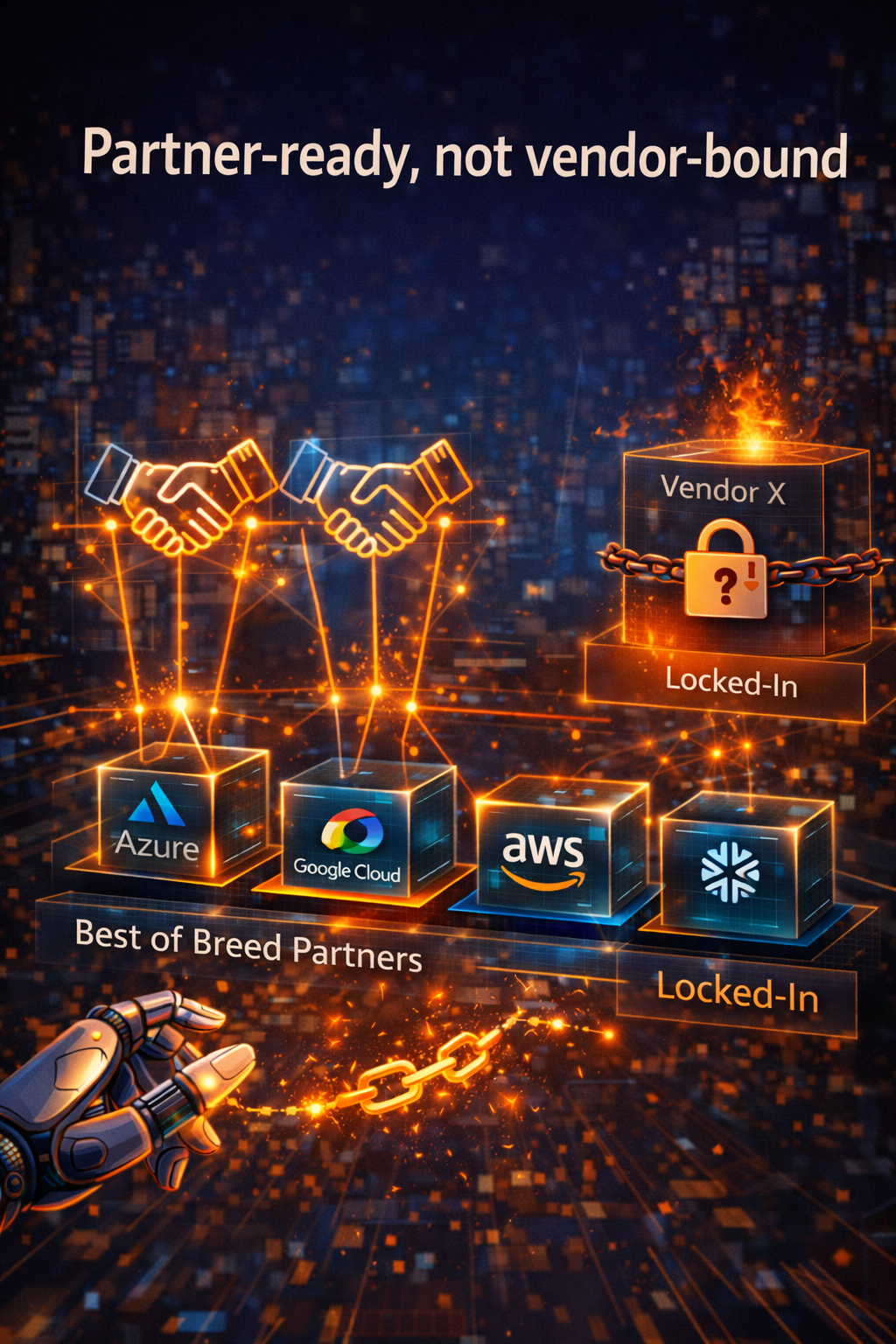
Why “AI platforms” stop working at scale
1) Platforms optimize creation. Enterprises need flow.
Platforms help you build “something.” Supply chains help you build “things”—repeatedly, safely, economically.
The difference is not philosophical. It’s operational:
- Platforms encourage teams to build in parallel.
- Supply chains encourage teams to reuse what already works.
In a platform-only world, you get a fast-growing portfolio of AI artifacts.
In a supply-chain world, you get a growing portfolio of standardized intelligence products.
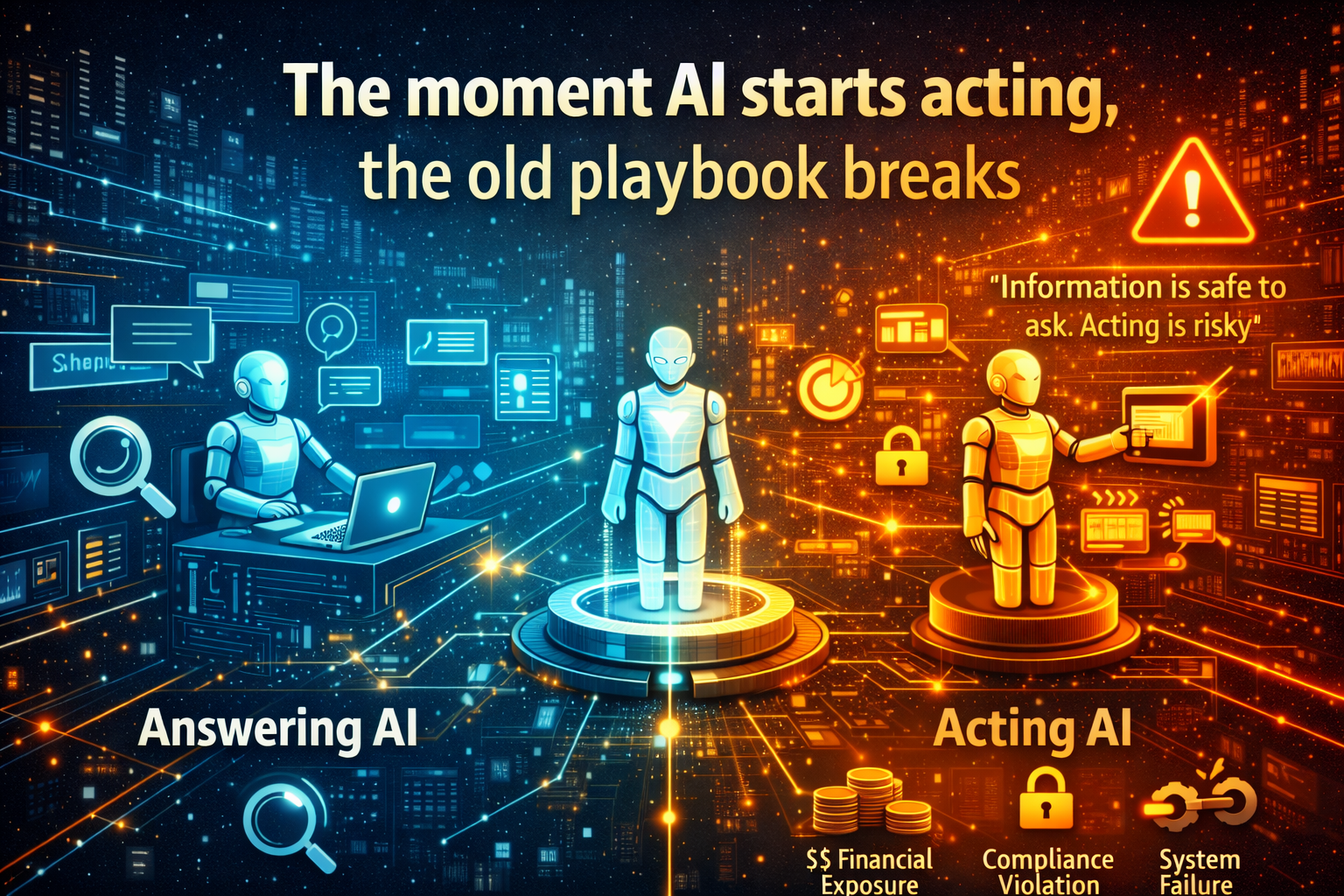
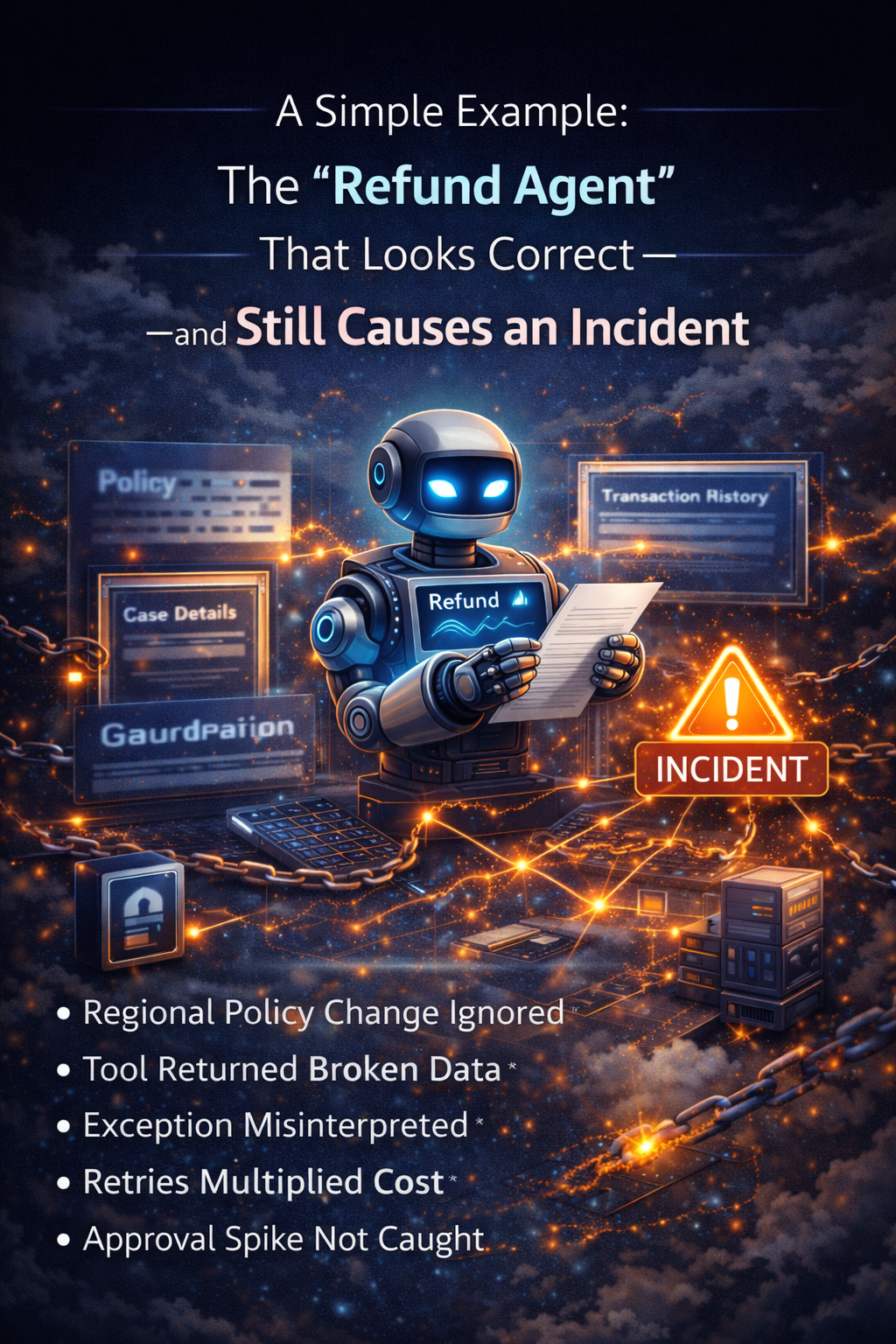
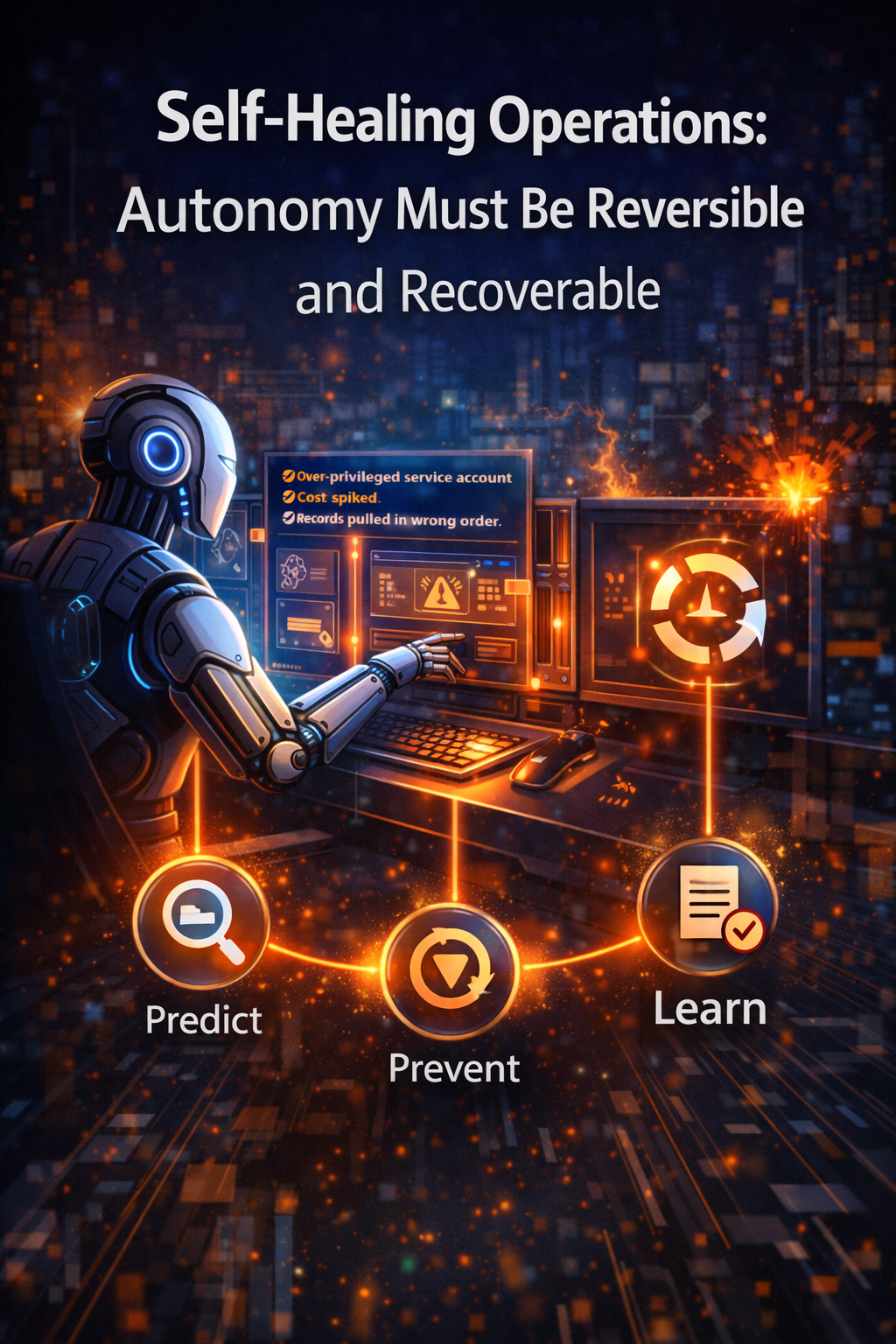
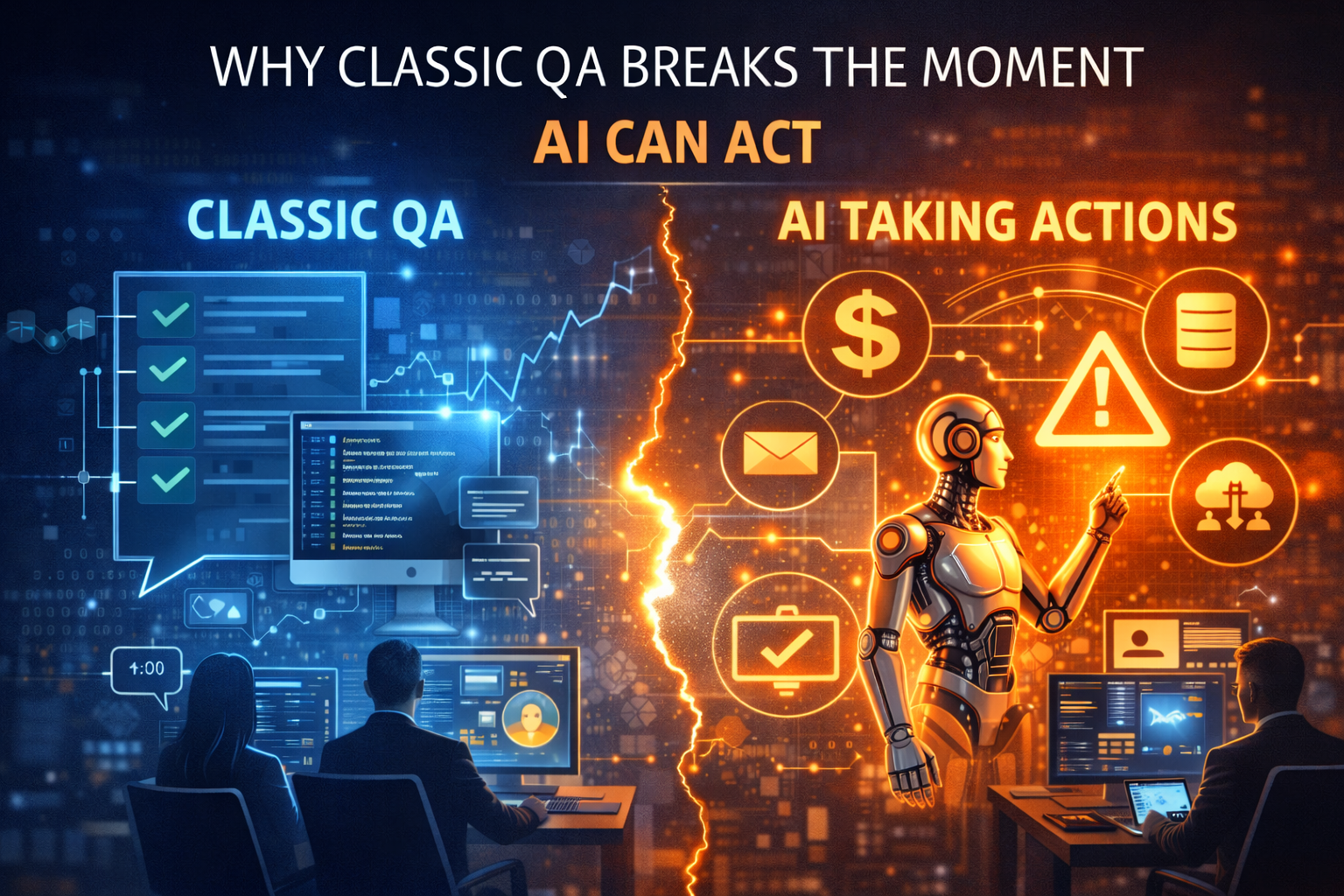
2) AI introduces failure modes that look like success—until it’s too late
Traditional software fails loudly (outages, errors). AI can fail quietly:
- It can be “helpful” while being noncompliant.
- It can increase speed while injecting risk.
- It can improve outcomes early while drifting later.
This is why lifecycle risk management matters. NIST’s AI Risk Management Framework emphasizes risk management across the AI lifecycle—design to deployment to ongoing operation. (NIST Publications)
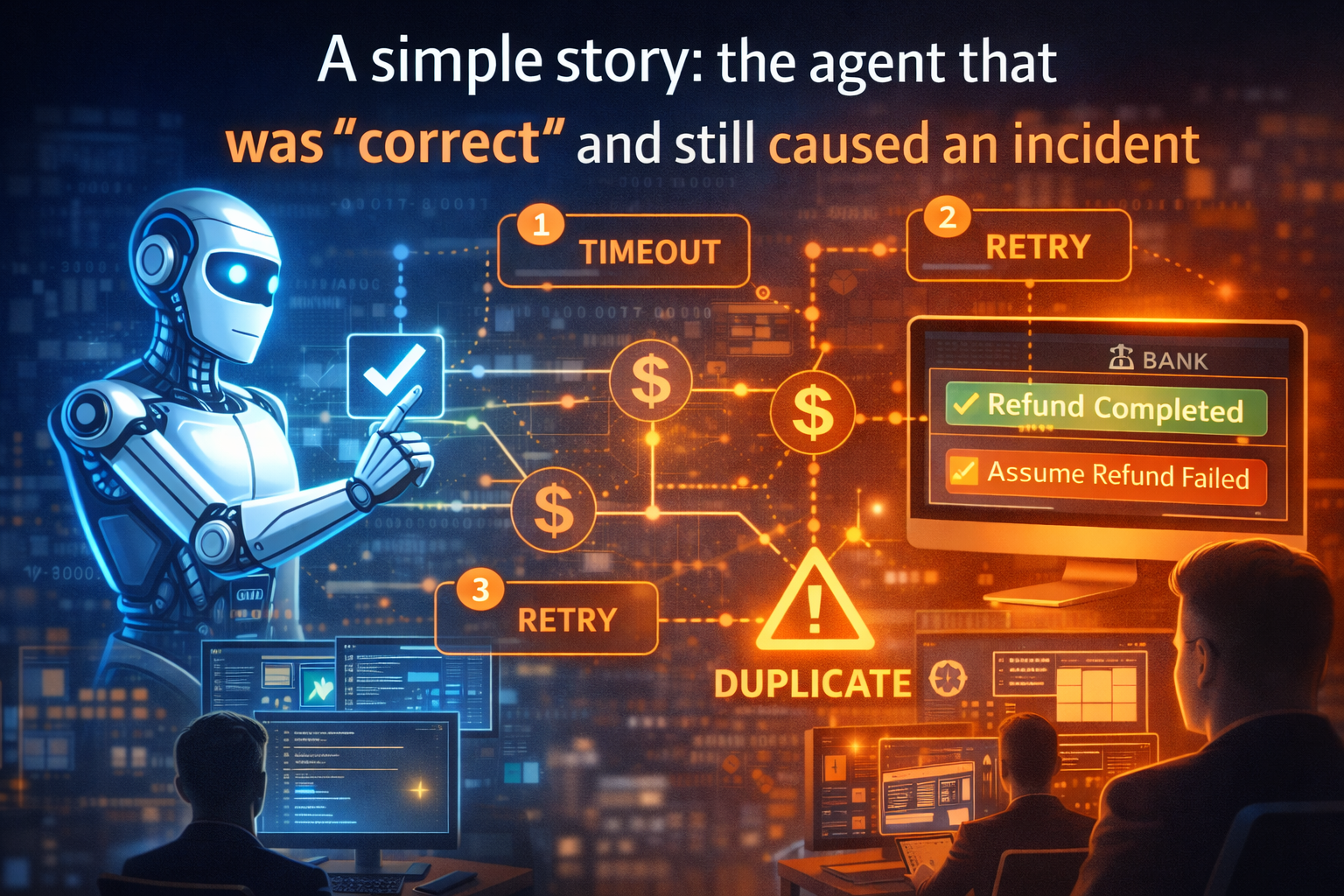
3) AI economics isn’t a reporting problem. It’s a control problem.
With LLMs and agents, usage patterns are cost patterns.
If an agent retries, expands context aggressively, or loops through tool calls, you can get “successful completions” and still lose financially.
That is why FinOps for AI has emerged: to make AI spending governable and optimizable as an operating practice (not an after-the-fact bill review). (FinOps Foundation)

The Intelligence Supply Chain: 7 stages that make AI industrial-grade
This is the practical model. Each stage is a failure mode if you ignore it—and a competitive advantage if you master it.
Stage 1: Sourcing — Inputs you can trust
In any supply chain, quality starts with raw materials.
In AI, “raw materials” are:
- policies and procedures
- approved knowledge and guidance
- tool access rules
- reference data
- escalation and exception logic
Simple example:
A support assistant can sound confident while violating a policy. Not because it’s malicious—because the policy was outdated, scattered, or ambiguous.
What mature organizations do:
They treat knowledge like governed inventory: owned, versioned, curated, and refreshed.
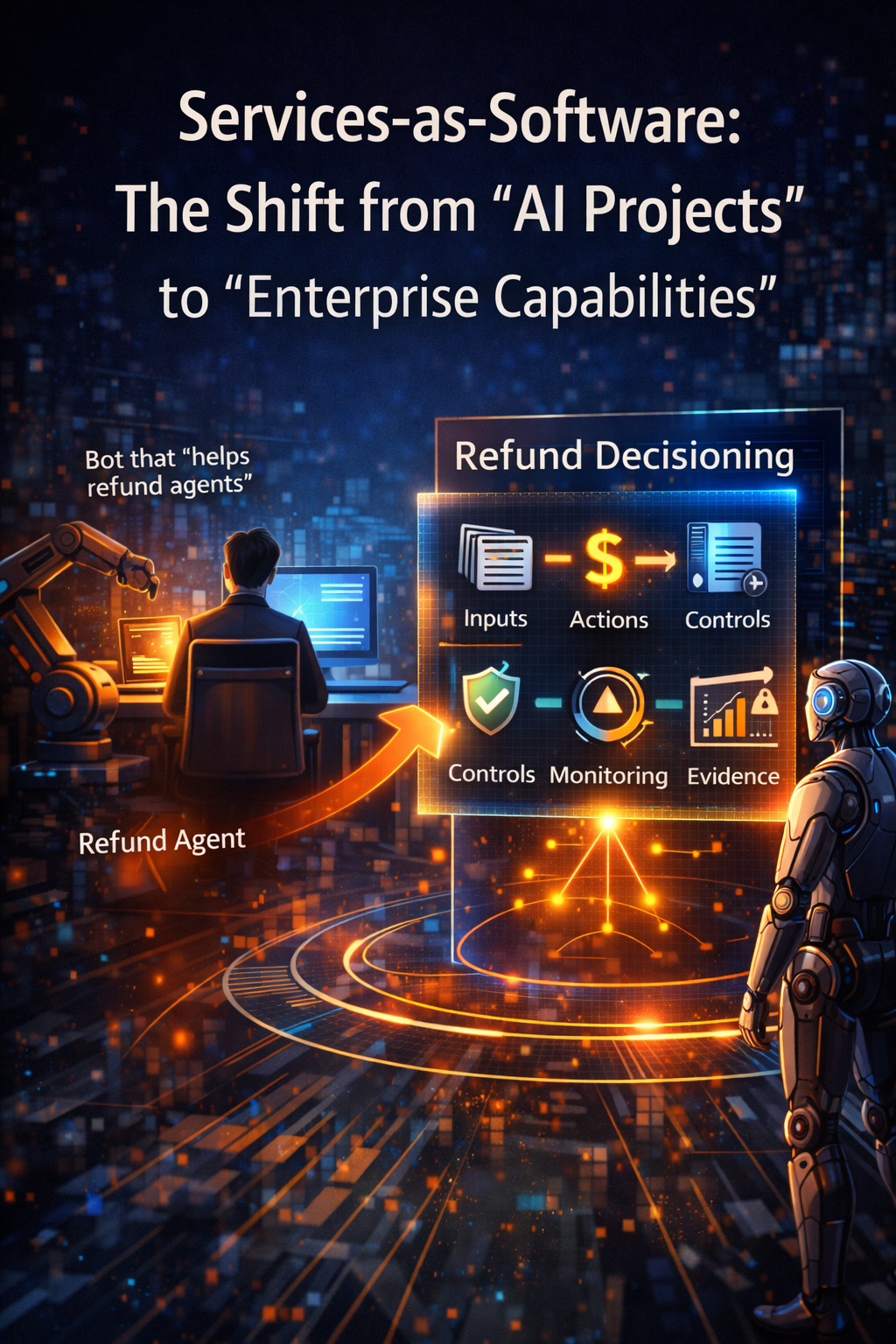
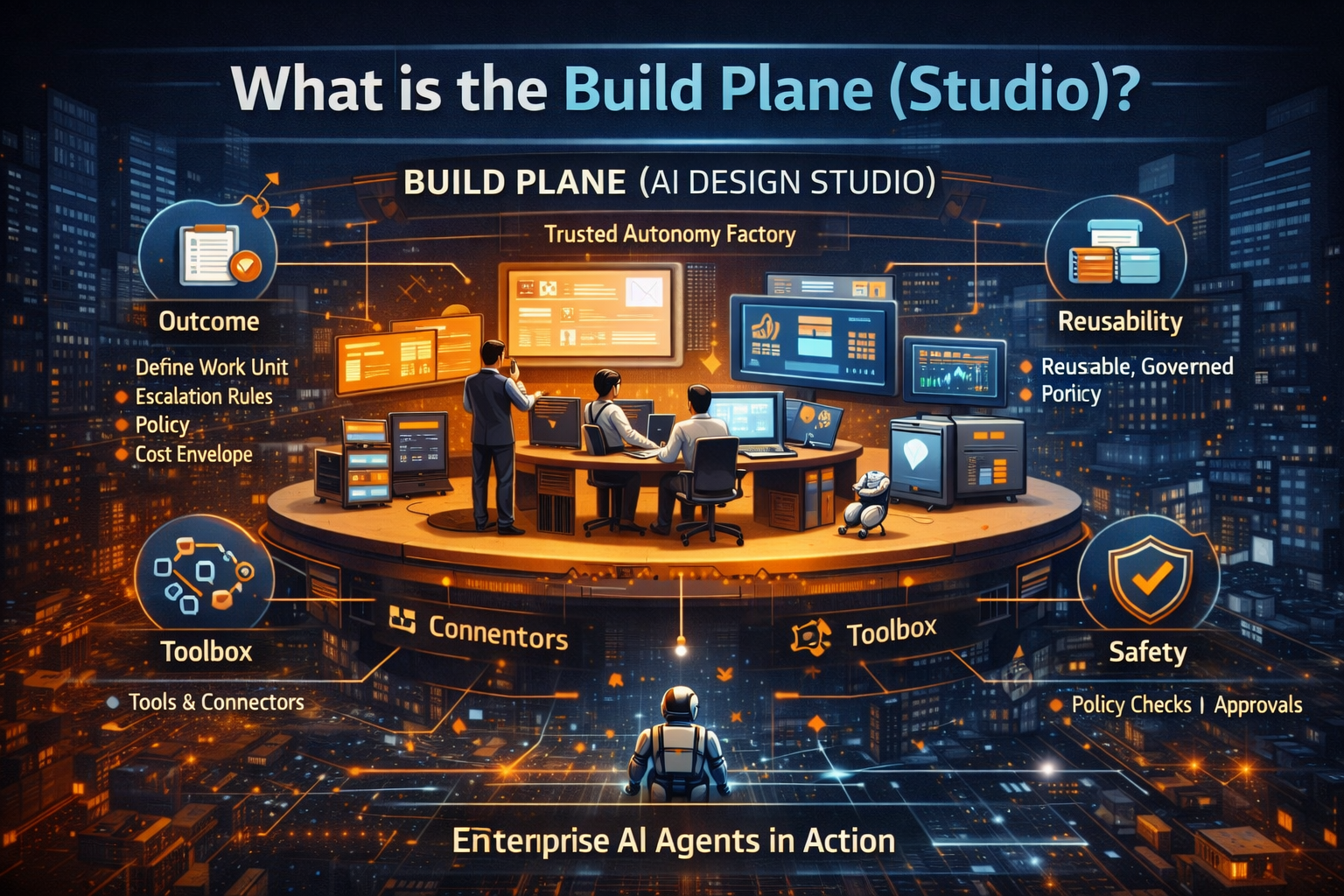
Stage 2: Design & Assembly — Build intelligence like a product line
Many teams stop at “prompting.” But supply chain thinking asks:
- Can this be reused?
- Can this be composed into larger workflows?
- Can this be policy-aware by default?
Simple example:
Instead of building “one agent per team,” you standardize components like:
- “Explain-before-act” for sensitive steps
- “Policy-check before execution”
- “Approval gate when confidence is low or action is high-impact”
- “Standard tool wrapper with logging, rate limits, and error handling”
This is the difference between artisanal AI and industrial AI.
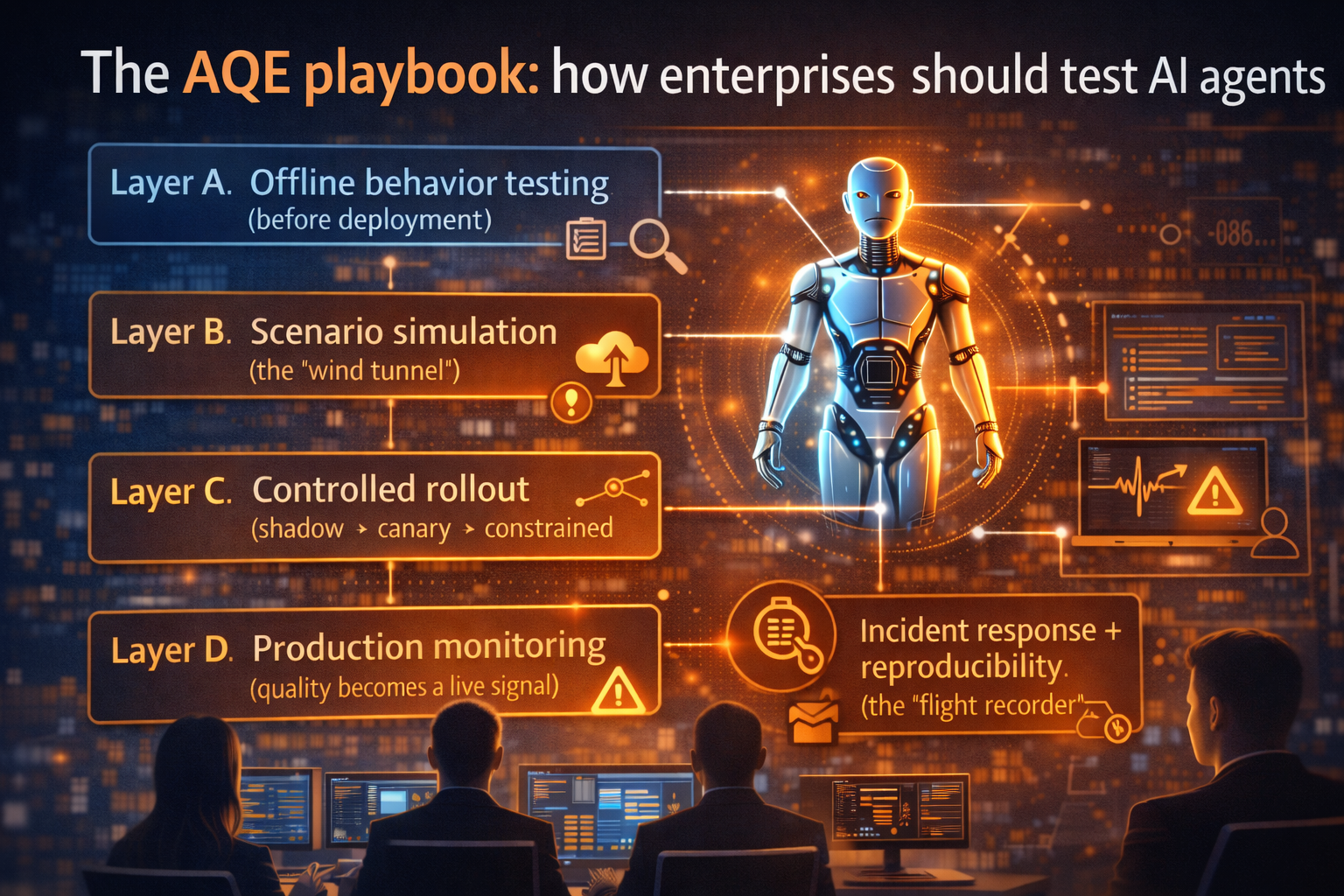
Stage 3: Quality Engineering — Test what matters in real operations
Classic tests ask: “Does it work?”
AI tests must ask: “Does it behave safely under variability?”
You test:
- policy compliance
- tool-call correctness
- robustness under ambiguous input
- safe failure behavior
- consistency across versions
Simple example:
An operations agent that can close incidents must be tested for:
- missing context
- conflicting signals
- tool timeouts
- edge cases where closure is prohibited
- escalation pathways
Not to make it perfect—to make it predictable.
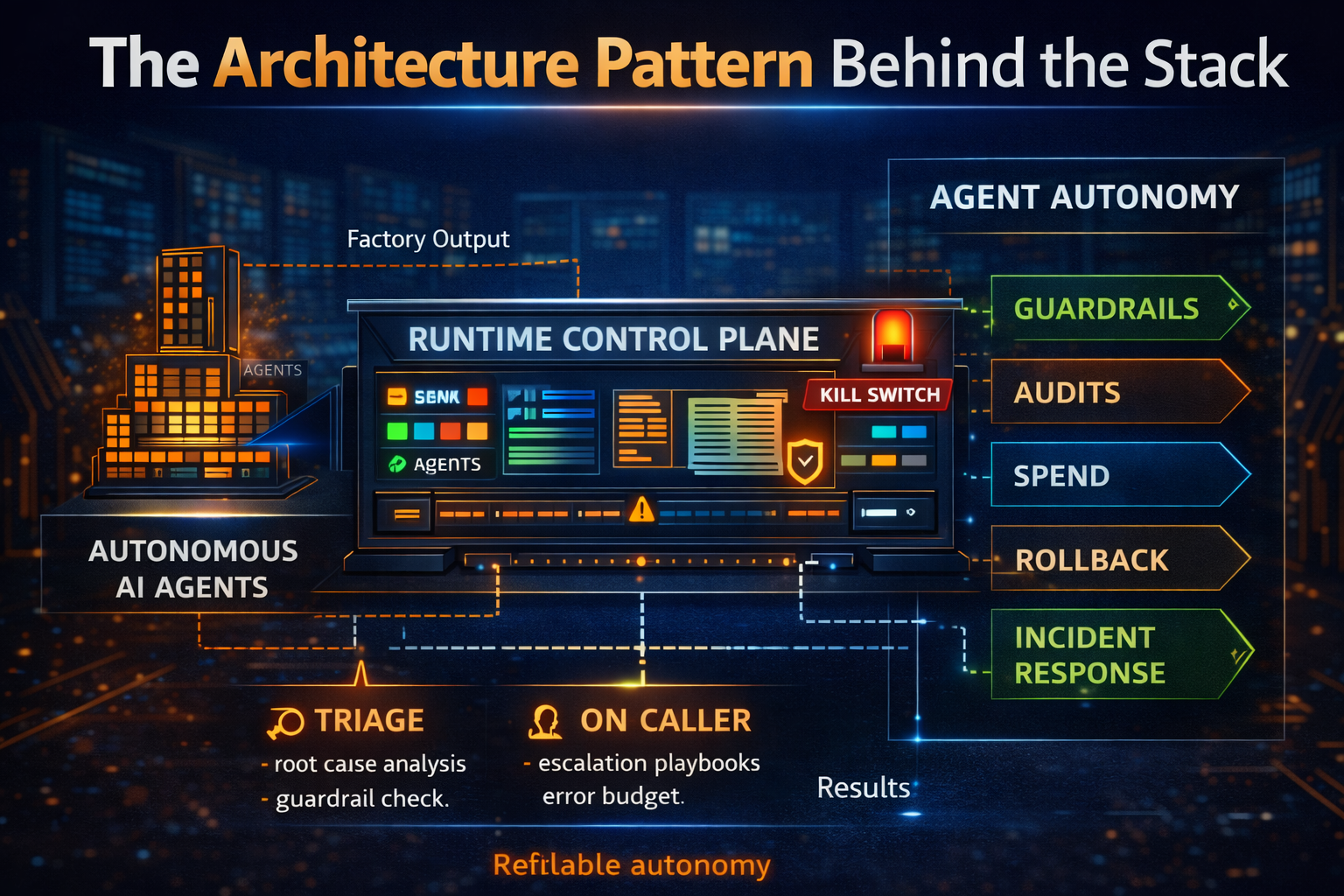
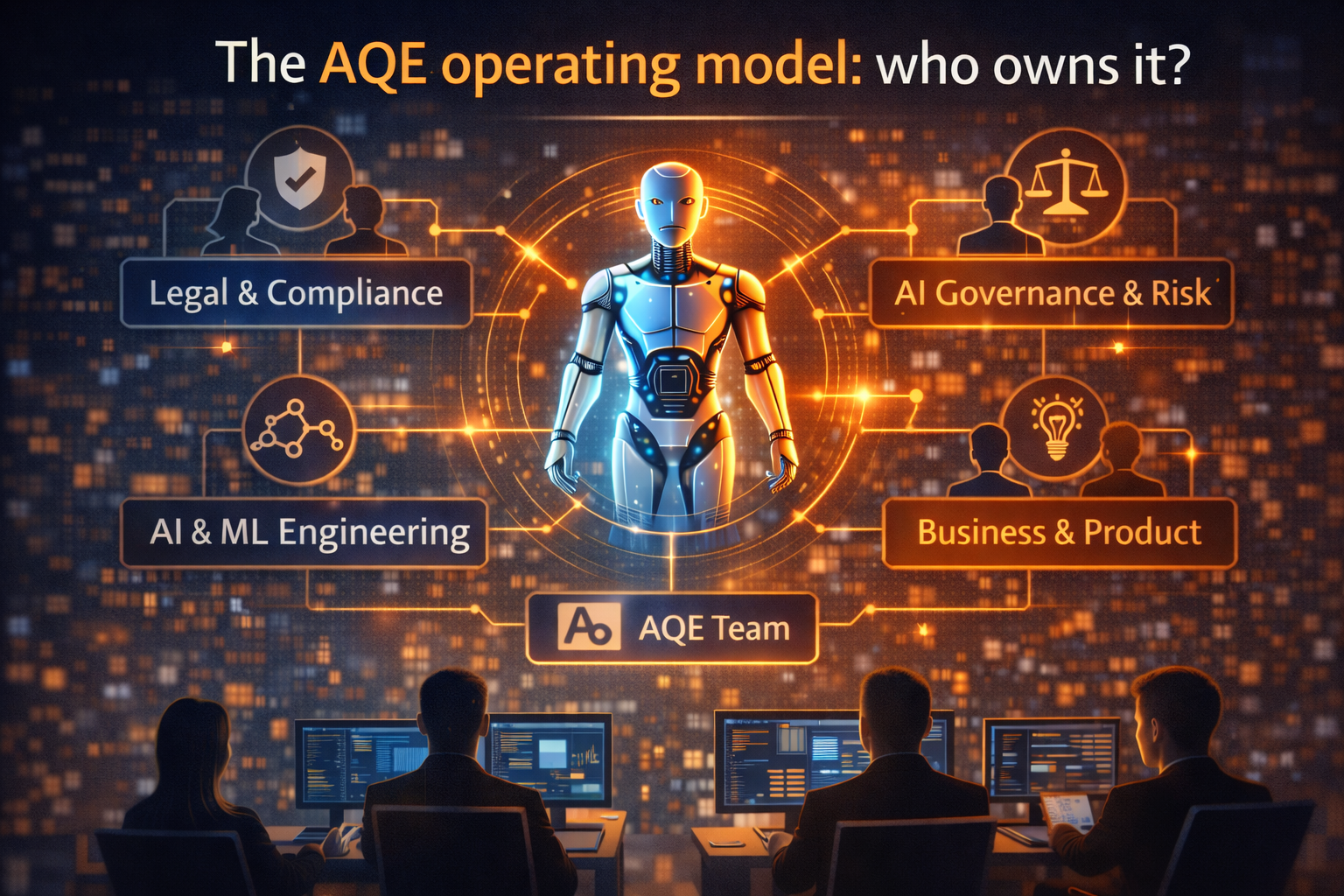
Stage 4: Guardrails & Governance — The rules of the factory floor
This is where most executive anxiety actually lives.
Guardrails include:
- identity and permissions
- least-privilege tool access
- policy enforcement
- audit trails
- human-in-the-loop gates
- escalation and kill switches
Simple example:
A procurement agent can draft a vendor email, but cannot send it without approval.
A finance assistant can prepare a reconciliation, but cannot post entries directly.
This is not bureaucracy.
This is what turns “AI that can act” into “AI that can act safely.”
Stage 5: AI FinOps & Cost Control — Make economics enforceable
Here’s the uncomfortable truth: AI cost surprises are rarely caused by one big decision. They’re caused by thousands of tiny defaults.
In a supply chain, you track cost per unit. In AI, you track cost per:
- workflow
- request type
- agent
- business outcome
- model choice
- tool invocation pattern
Simple example:
Two workflows appear identical:
- Workflow A: lightweight classification + retrieval + one response
- Workflow B: larger model + multiple tool calls + retries + aggressive context expansion
Workflow B quietly becomes your cost sink—unless cost controls are designed into the system.
FinOps for AI exists to operationalize exactly this: visibility, optimization, governance, and value tracking around AI spend. (FinOps Foundation)
Stage 6: Deployment & Orchestration — Ship intelligence safely and consistently
Orchestration means:
- routing tasks to the right agent/model
- sequencing steps across tools
- managing retries and fallbacks
- preserving context across steps
- enforcing guardrails at every hop
Simple example:
A dispute-resolution flow orchestrates:
- classify request
- retrieve policy + context
- propose options
- policy-check options
- draft response
- approval if needed
- execute update in system
Without orchestration, your enterprise gets a pile of demos.
With orchestration, you get an operating system for intelligent work.
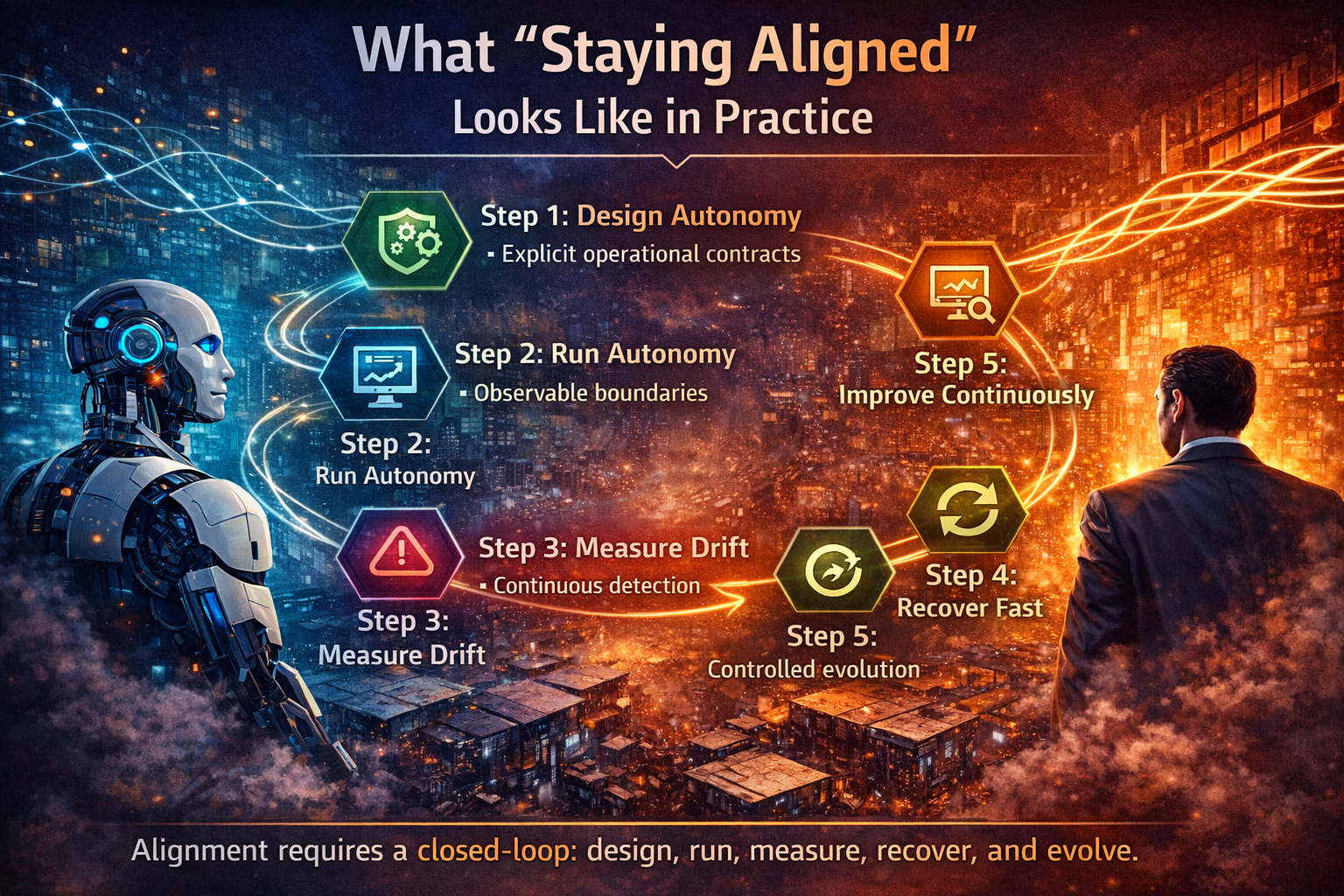
Stage 7: Monitoring, Drift Handling, and Recall — Operate like a living system
If intelligence is a product, you need operations discipline:
- continuous monitoring
- drift detection
- policy refresh cycles
- prompt/tool updates
- rollback when behavior changes
NIST’s lifecycle view exists for a reason: risk evolves after deployment. (NIST Publications)
Simple example:
A policy changes. The agent continues following the old rule.
Nothing breaks technically. But compliance risk rises—and outcomes drift.
A supply chain ensures updates flow through knowledge → tests → guardrails → redeployments → monitoring.

The executive payoff: three wins that get funded
1) Speed without chaos
You ship faster because teams reuse standard components:
policy checks, tool wrappers, evaluation suites, deployment templates, observability, approvals.
2) Predictable economics
Cost becomes a control plane, not an argument after the bill arrives:
budgets per workflow, throttles, routing rules, thresholds, exception handling.
3) Trust at scale
Trust isn’t “the model is smart.”
Trust is “the system is governed.”
Audit trails. Evidence. Permissions. Policy enforcement. Rollback.
That is what turns AI into enterprise-grade capability.

A simple scenario that makes the shift inevitable
Three teams build AI independently:
- Support builds a customer assistant
- Operations builds an incident agent
- Finance builds a reconciliation assistant
All three require the same enterprise primitives:
- identity and permissions
- audit trail format
- policy checker
- tool-call wrapper
- cost dashboards
- evaluation harness
- escalation/rollback behavior
Without a supply chain, each team reimplements these differently.
Result:
- inconsistent compliance
- duplicated effort
- unpredictable cost
- governance that cannot scale
With a supply chain, those primitives become shared infrastructure. Teams assemble solutions rather than reinventing controls.
That’s the difference between an “AI platform” and an “intelligence-producing enterprise.”

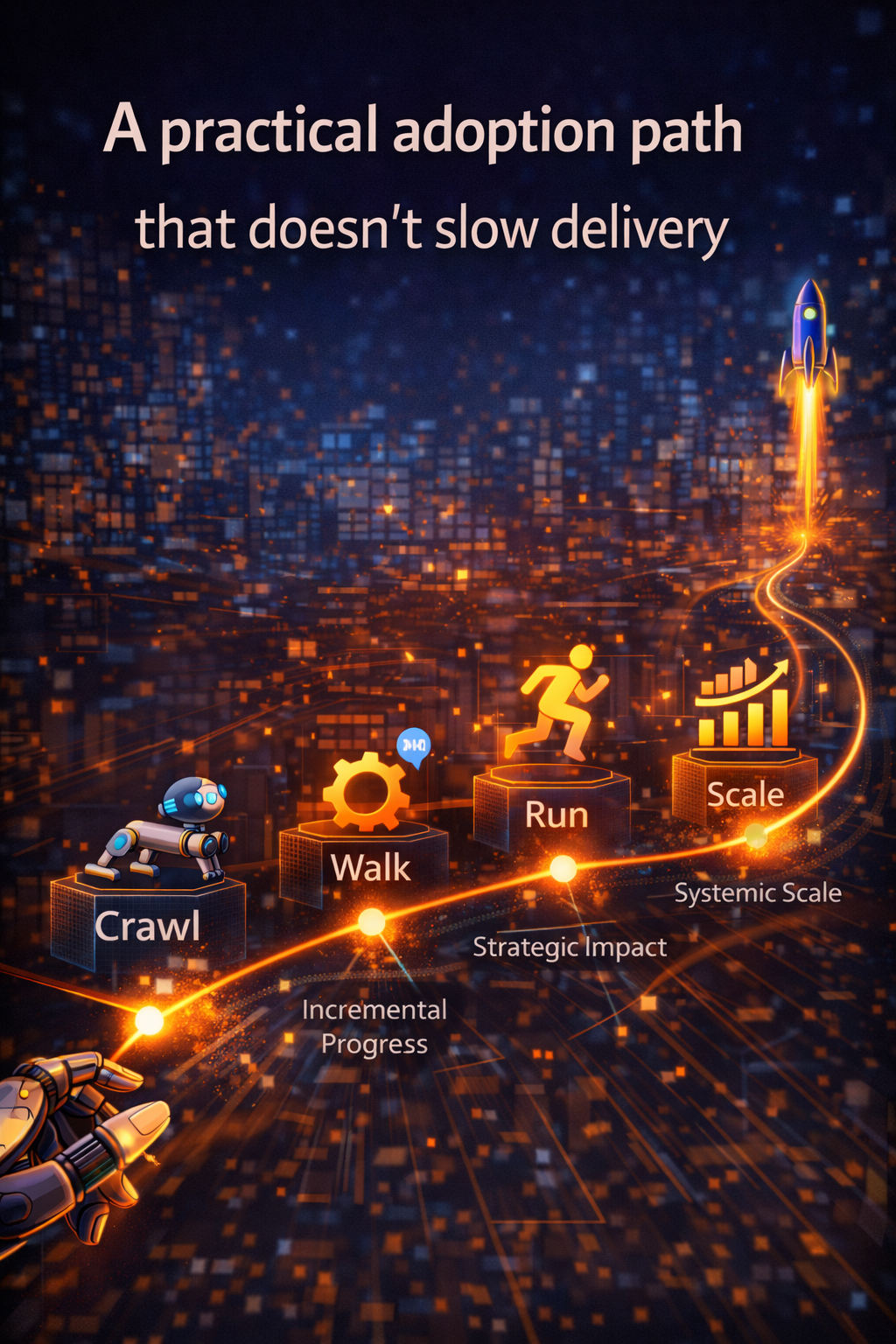
How to start (without boiling the ocean)
How to start (without boiling the ocean)
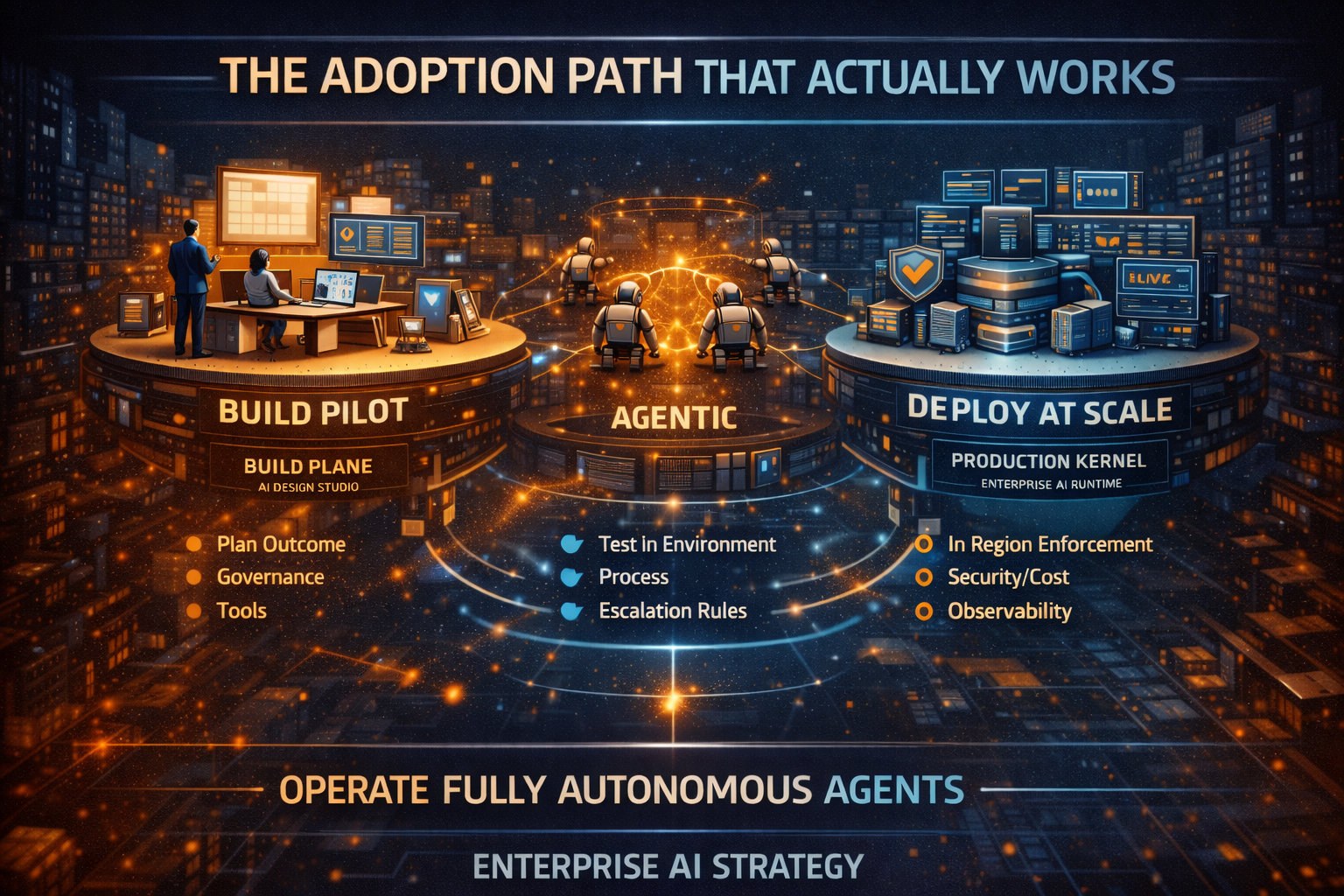
Pick one workflow where AI can take action (not just answer questions). Then implement a “minimum viable supply chain”:
- Sourcing: identify authoritative inputs + owner
- Assembly: build reusable components (policy check, approval gate, tool wrapper)
- QE: create a small test suite (policy, tool correctness, ambiguity handling)
- Guardrails: enforce least privilege + audit trail
- FinOps: track cost per successful outcome + set budgets
- Orchestration: add routing and fallbacks
- Ops: monitor drift + define rollback triggers
You’re not trying to “finish the architecture.”
You’re proving the operating model.

What to measure (signals that prove maturity)
- Reuse rate (are we scaling through reuse or cloning?)
- Cost per successful outcome (not cost per call)
- Policy violation rate (measured, not assumed)
- Escalation rate (where humans intervene and why)
- Time-to-update (how fast policy/tool/model changes propagate safely)
- Rollback readiness (how quickly you can reverse behavior under uncertainty)
These metrics tell you if AI is industrializing—or fragmenting.

Conclusion
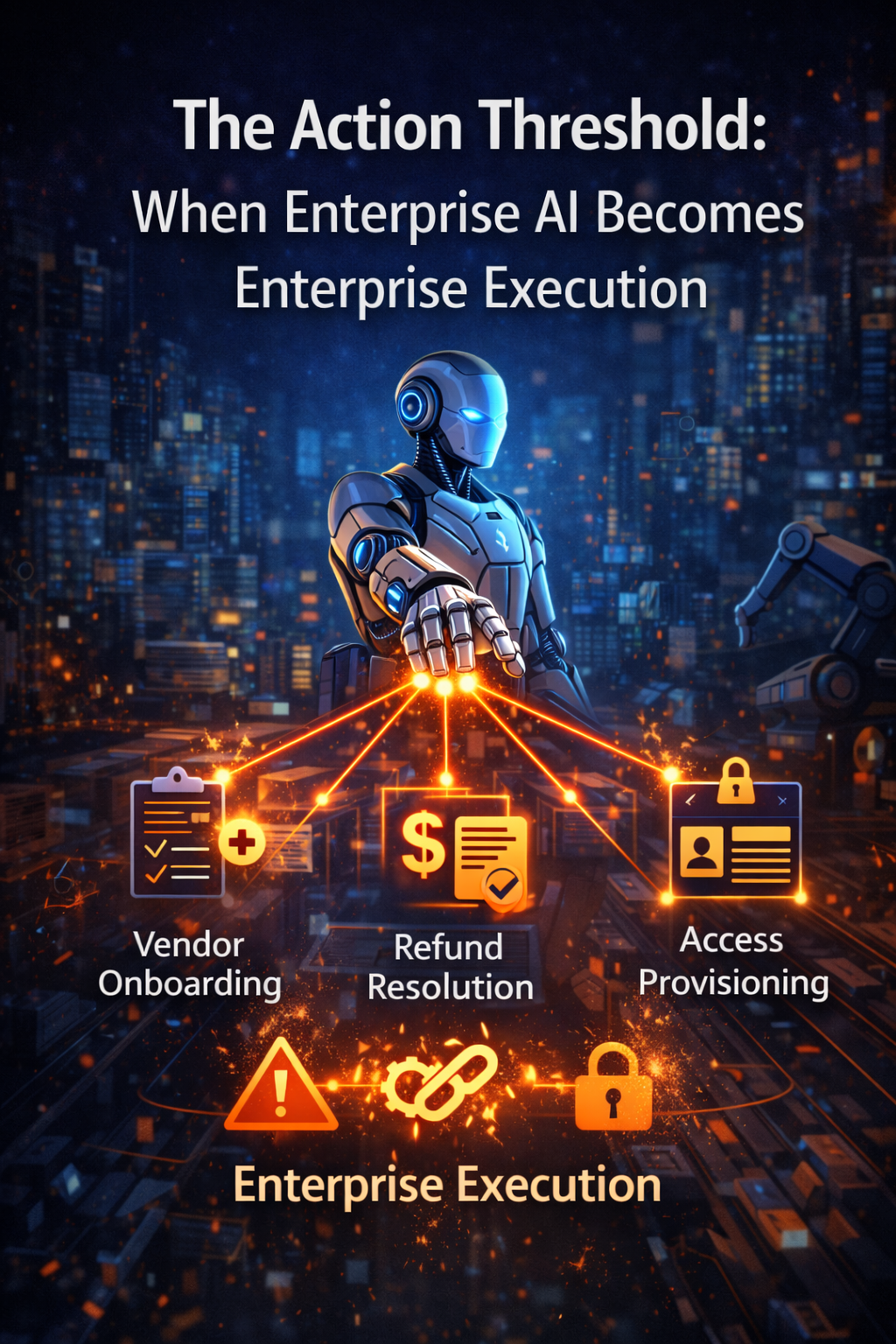
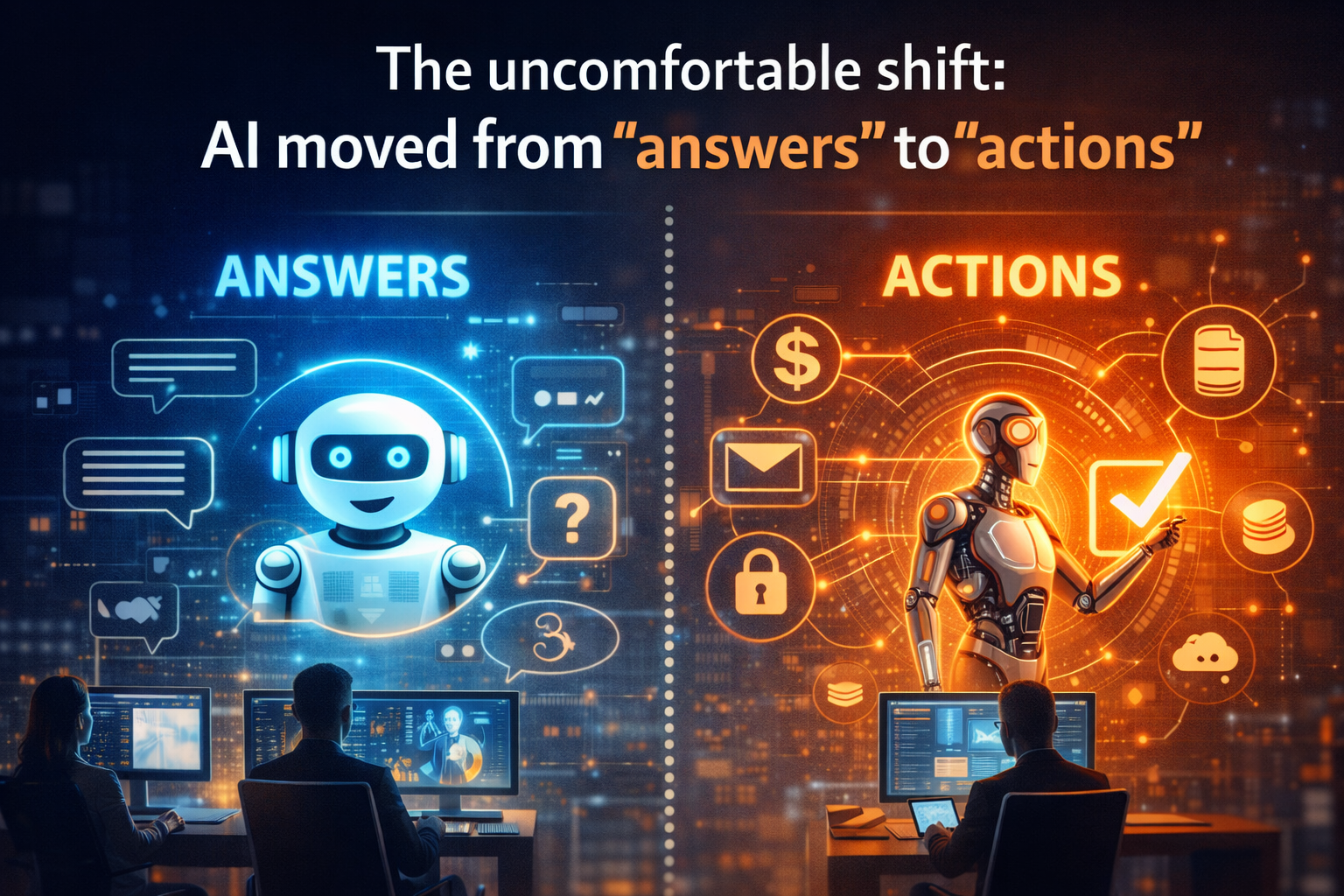
What’s happening: Enterprises are moving from “AI platforms” to intelligence supply chains because AI is shifting from answering to acting.
Why now: Agentic AI introduces quiet failure modes—drift, cost explosions, and policy violations—that don’t show up in demos. Market signals reinforce this: Gartner predicts over 40% of agentic AI projects may be canceled by end of 2027 due to cost, value ambiguity, and risk controls. (Gartner)
What wins: The winners will treat intelligence like a product line: sourced, assembled, tested, governed, cost-controlled, orchestrated, monitored, and continuously improved.
The strategic advantage: Not smarter models—manufactured intelligence.
FAQ
What is an intelligence supply chain in enterprise AI?
An intelligence supply chain is an end-to-end system for producing and operating AI capabilities with predictable quality, governance, cost control, and reuse—like a production line for intelligence.
Why are agentic AI projects at risk of cancellation?
Many struggle with escalating operational costs, unclear business value, and inadequate risk controls—especially when moving from pilots to production. Gartner forecasts over 40% cancellations by end of 2027. (Gartner)
How is an intelligence supply chain different from an AI platform?
An AI platform helps you build AI. An intelligence supply chain ensures AI flows through standardized sourcing, testing, governance, cost controls, deployment, monitoring, and continuous improvement—so it scales safely.
Do we need to train our own models to implement this?
No. This is model-agnostic. The core value is the enterprise operating system around models: guardrails, orchestration, observability, governance, and cost management.
What is FinOps for AI and why does it matter?
FinOps for AI applies operational cost governance to AI workloads—tracking spend drivers, optimizing usage, and aligning AI investment with measurable value. (FinOps Foundation)
How does the NIST AI RMF relate to this approach?
NIST AI RMF emphasizes managing AI risks across the lifecycle (including ongoing monitoring and governance), which aligns directly with supply chain thinking. (NIST Publications)
Glossary
- Agentic AI: AI systems that can take actions via tools and workflows, not just generate text.
- Orchestration: Coordinating multi-step tasks across models, tools, approvals, and fallbacks.
- Guardrails: Controls that keep AI within policy, permissions, and safety boundaries.
- AI FinOps: Continuous governance and optimization of AI costs and value. (FinOps Foundation)
- Drift: When real-world changes cause AI outputs or actions to degrade over time.
- Lifecycle risk management: Managing AI risks from design through deployment and ongoing operation. (NIST Publications)
- Reuse: Building standardized components once and assembling solutions repeatedly.
References and further reading (credible, lightweight)
- Gartner press release on agentic AI cancellations forecast (June 2025). (Gartner)
- NIST AI Risk Management Framework (AI RMF 1.0) and overview page. (NIST Publications)
- FinOps Foundation: FinOps for AI overview and topic hub; FinOps guidance on AI value. (FinOps Foundation)
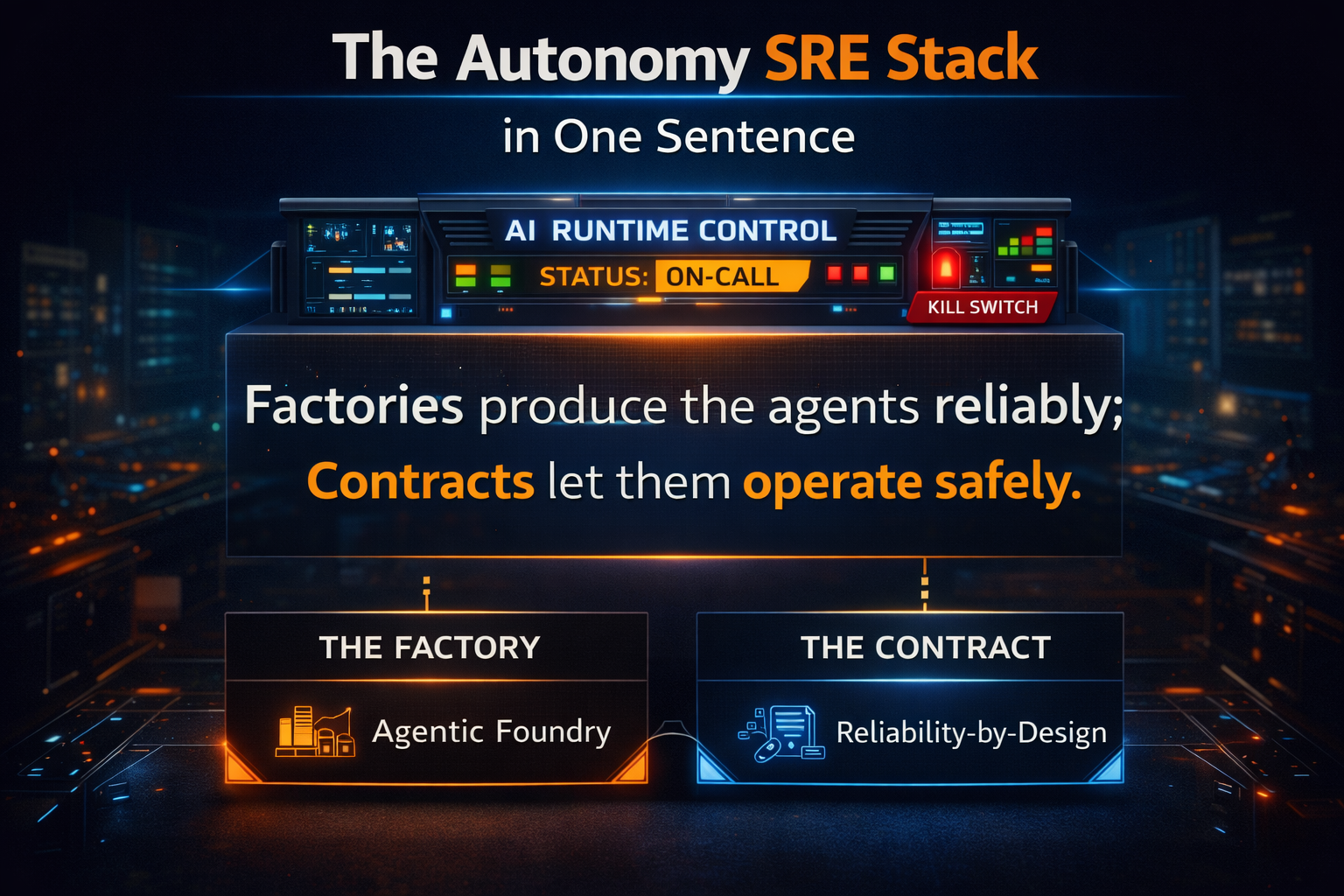
- The Autonomy SRE Stack: How Enterprises Run AI Autonomy Safely, Reliably, and at Scale – Raktim Singh
- The Agentic Foundry: How Enterprises Scale AI Autonomy Without Losing Control, Trust, or Economics – Raktim Singh
- The One Enterprise AI Stack CIOs Are Converging On: Why Operability, Not Intelligence, Is the New Advantage – Raktim Singh
- Studio-to-Runtime: Why Enterprise AI Fails Without a Build Plane and a Production Kernel – Raktim Singh
- Why Autonomous AI Breaks in Production: And Why Enterprises Need an AI Control Tower to Run It at Scale | by RAKTIM SINGH | Dec, 2025 | Medium
- Why Autonomous AI Fails in Production — and What CIOs Must Do to Control It: By Raktim Singh
- Enterprise IT Is Becoming an App Store: From Projects to Services-as-Software: By Raktim Singh
- The AI Platform War Is Over: Why Enterprises Must Build an AI Fabric—Not an Agent Zoo – Raktim Singh